diff --git a/.github/workflows/test-sample-go.yml b/.github/workflows/test-sample-go.yml
index 08e1c9a1984..035ddb0aea4 100644
--- a/.github/workflows/test-sample-go.yml
+++ b/.github/workflows/test-sample-go.yml
@@ -25,8 +25,10 @@ jobs:
KUSTOMIZATION_FILE_PATH="testdata/project-v4/config/default/kustomization.yaml"
sed -i '25s/^#//' $KUSTOMIZATION_FILE_PATH
sed -i '27s/^#//' $KUSTOMIZATION_FILE_PATH
- sed -i '42s/^#//' $KUSTOMIZATION_FILE_PATH
- sed -i '46,143s/^#//' $KUSTOMIZATION_FILE_PATH
+ sed -i '33s/^#//' $KUSTOMIZATION_FILE_PATH
+ sed -i '38s/^#//' $KUSTOMIZATION_FILE_PATH
+ sed -i '47s/^#//' $KUSTOMIZATION_FILE_PATH
+ sed -i '51,147s/^#//' $KUSTOMIZATION_FILE_PATH
- name: Test
run: |
diff --git a/docs/book/src/component-config-tutorial/testdata/project/config/default/kustomization.yaml b/docs/book/src/component-config-tutorial/testdata/project/config/default/kustomization.yaml
index e0e588792cf..421174a10b9 100644
--- a/docs/book/src/component-config-tutorial/testdata/project/config/default/kustomization.yaml
+++ b/docs/book/src/component-config-tutorial/testdata/project/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# Mount the controller config file for loading manager configurations
# through a ComponentConfig type
diff --git a/docs/book/src/component-config-tutorial/testdata/project/config/default/manager_auth_proxy_patch.yaml b/docs/book/src/component-config-tutorial/testdata/project/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 74c49152afb..00000000000
--- a/docs/book/src/component-config-tutorial/testdata/project/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,34 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
diff --git a/docs/book/src/component-config-tutorial/testdata/project/config/default/manager_metrics_patch.yaml b/docs/book/src/component-config-tutorial/testdata/project/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/docs/book/src/component-config-tutorial/testdata/project/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/docs/book/src/component-config-tutorial/testdata/project/config/prometheus/monitor.yaml b/docs/book/src/component-config-tutorial/testdata/project/config/prometheus/monitor.yaml
index 893610e2014..ee7ee7abd33 100644
--- a/docs/book/src/component-config-tutorial/testdata/project/config/prometheus/monitor.yaml
+++ b/docs/book/src/component-config-tutorial/testdata/project/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/docs/book/src/component-config-tutorial/testdata/project/config/rbac/kustomization.yaml b/docs/book/src/component-config-tutorial/testdata/project/config/rbac/kustomization.yaml
index 9f6506d4c5b..de9ecfd0693 100644
--- a/docs/book/src/component-config-tutorial/testdata/project/config/rbac/kustomization.yaml
+++ b/docs/book/src/component-config-tutorial/testdata/project/config/rbac/kustomization.yaml
@@ -10,15 +10,15 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
# For each CRD, "Editor" and "Viewer" roles are scaffolded by
# default, aiding admins in cluster management. Those roles are
# not used by the Project itself. You can comment the following lines
# if you do not want those helpers be installed with your Project.
- projectconfig_editor_role.yaml
- projectconfig_viewer_role.yaml
+
diff --git a/docs/book/src/component-config-tutorial/testdata/project/config/rbac/auth_proxy_client_clusterrole.yaml b/docs/book/src/component-config-tutorial/testdata/project/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from docs/book/src/component-config-tutorial/testdata/project/config/rbac/auth_proxy_client_clusterrole.yaml
rename to docs/book/src/component-config-tutorial/testdata/project/config/rbac/metrics_client_cluster_role.yaml
diff --git a/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/auth_proxy_role.yaml b/docs/book/src/component-config-tutorial/testdata/project/config/rbac/metrics_role.yaml
similarity index 94%
rename from docs/book/src/cronjob-tutorial/testdata/project/config/rbac/auth_proxy_role.yaml
rename to docs/book/src/component-config-tutorial/testdata/project/config/rbac/metrics_role.yaml
index 17e0a11d32b..2265a70613e 100644
--- a/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/auth_proxy_role.yaml
+++ b/docs/book/src/component-config-tutorial/testdata/project/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/docs/book/src/getting-started/testdata/project/config/rbac/auth_proxy_role_binding.yaml b/docs/book/src/component-config-tutorial/testdata/project/config/rbac/metrics_role_binding.yaml
similarity index 86%
rename from docs/book/src/getting-started/testdata/project/config/rbac/auth_proxy_role_binding.yaml
rename to docs/book/src/component-config-tutorial/testdata/project/config/rbac/metrics_role_binding.yaml
index e1f50c3178a..e94f3a89e4c 100644
--- a/docs/book/src/getting-started/testdata/project/config/rbac/auth_proxy_role_binding.yaml
+++ b/docs/book/src/component-config-tutorial/testdata/project/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/docs/book/src/component-config-tutorial/testdata/project/config/rbac/auth_proxy_service.yaml b/docs/book/src/component-config-tutorial/testdata/project/config/rbac/metrics_service.yaml
similarity index 100%
rename from docs/book/src/component-config-tutorial/testdata/project/config/rbac/auth_proxy_service.yaml
rename to docs/book/src/component-config-tutorial/testdata/project/config/rbac/metrics_service.yaml
diff --git a/docs/book/src/cronjob-tutorial/testdata/project/config/default/kustomization.yaml b/docs/book/src/cronjob-tutorial/testdata/project/config/default/kustomization.yaml
index e445fec445d..ba2b3d2cbd3 100644
--- a/docs/book/src/cronjob-tutorial/testdata/project/config/default/kustomization.yaml
+++ b/docs/book/src/cronjob-tutorial/testdata/project/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# [WEBHOOK] To enable webhook, uncomment all the sections with [WEBHOOK] prefix including the one in
# crd/kustomization.yaml
diff --git a/docs/book/src/cronjob-tutorial/testdata/project/config/default/manager_auth_proxy_patch.yaml b/docs/book/src/cronjob-tutorial/testdata/project/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 1064aa49c80..00000000000
--- a/docs/book/src/cronjob-tutorial/testdata/project/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,55 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- affinity:
- nodeAffinity:
- requiredDuringSchedulingIgnoredDuringExecution:
- nodeSelectorTerms:
- - matchExpressions:
- - key: kubernetes.io/arch
- operator: In
- values:
- - amd64
- - arm64
- - ppc64le
- - s390x
- - key: kubernetes.io/os
- operator: In
- values:
- - linux
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
diff --git a/docs/book/src/cronjob-tutorial/testdata/project/config/default/manager_metrics_patch.yaml b/docs/book/src/cronjob-tutorial/testdata/project/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/docs/book/src/cronjob-tutorial/testdata/project/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/docs/book/src/cronjob-tutorial/testdata/project/config/prometheus/monitor.yaml b/docs/book/src/cronjob-tutorial/testdata/project/config/prometheus/monitor.yaml
index 893610e2014..ee7ee7abd33 100644
--- a/docs/book/src/cronjob-tutorial/testdata/project/config/prometheus/monitor.yaml
+++ b/docs/book/src/cronjob-tutorial/testdata/project/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/kustomization.yaml b/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/kustomization.yaml
index 8db606e9e72..fbe26d33c8f 100644
--- a/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/kustomization.yaml
+++ b/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/kustomization.yaml
@@ -10,15 +10,15 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
# For each CRD, "Editor" and "Viewer" roles are scaffolded by
# default, aiding admins in cluster management. Those roles are
# not used by the Project itself. You can comment the following lines
# if you do not want those helpers be installed with your Project.
- cronjob_editor_role.yaml
- cronjob_viewer_role.yaml
+
diff --git a/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/auth_proxy_client_clusterrole.yaml b/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from docs/book/src/cronjob-tutorial/testdata/project/config/rbac/auth_proxy_client_clusterrole.yaml
rename to docs/book/src/cronjob-tutorial/testdata/project/config/rbac/metrics_client_cluster_role.yaml
diff --git a/docs/book/src/component-config-tutorial/testdata/project/config/rbac/auth_proxy_role.yaml b/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/metrics_role.yaml
similarity index 94%
rename from docs/book/src/component-config-tutorial/testdata/project/config/rbac/auth_proxy_role.yaml
rename to docs/book/src/cronjob-tutorial/testdata/project/config/rbac/metrics_role.yaml
index 17e0a11d32b..2265a70613e 100644
--- a/docs/book/src/component-config-tutorial/testdata/project/config/rbac/auth_proxy_role.yaml
+++ b/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/docs/book/src/component-config-tutorial/testdata/project/config/rbac/auth_proxy_role_binding.yaml b/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/metrics_role_binding.yaml
similarity index 86%
rename from docs/book/src/component-config-tutorial/testdata/project/config/rbac/auth_proxy_role_binding.yaml
rename to docs/book/src/cronjob-tutorial/testdata/project/config/rbac/metrics_role_binding.yaml
index e1f50c3178a..e94f3a89e4c 100644
--- a/docs/book/src/component-config-tutorial/testdata/project/config/rbac/auth_proxy_role_binding.yaml
+++ b/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/auth_proxy_service.yaml b/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/metrics_service.yaml
similarity index 100%
rename from docs/book/src/cronjob-tutorial/testdata/project/config/rbac/auth_proxy_service.yaml
rename to docs/book/src/cronjob-tutorial/testdata/project/config/rbac/metrics_service.yaml
diff --git a/docs/book/src/getting-started/testdata/project/config/default/kustomization.yaml b/docs/book/src/getting-started/testdata/project/config/default/kustomization.yaml
index d851be9cae7..32c1863fbc5 100644
--- a/docs/book/src/getting-started/testdata/project/config/default/kustomization.yaml
+++ b/docs/book/src/getting-started/testdata/project/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# [WEBHOOK] To enable webhook, uncomment all the sections with [WEBHOOK] prefix including the one in
# crd/kustomization.yaml
diff --git a/docs/book/src/getting-started/testdata/project/config/default/manager_auth_proxy_patch.yaml b/docs/book/src/getting-started/testdata/project/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 4c3c27602f5..00000000000
--- a/docs/book/src/getting-started/testdata/project/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,39 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
diff --git a/docs/book/src/getting-started/testdata/project/config/default/manager_metrics_patch.yaml b/docs/book/src/getting-started/testdata/project/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/docs/book/src/getting-started/testdata/project/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/docs/book/src/getting-started/testdata/project/config/prometheus/monitor.yaml b/docs/book/src/getting-started/testdata/project/config/prometheus/monitor.yaml
index 893610e2014..ee7ee7abd33 100644
--- a/docs/book/src/getting-started/testdata/project/config/prometheus/monitor.yaml
+++ b/docs/book/src/getting-started/testdata/project/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/docs/book/src/getting-started/testdata/project/config/rbac/kustomization.yaml b/docs/book/src/getting-started/testdata/project/config/rbac/kustomization.yaml
index 3dc289427b8..67272c849a9 100644
--- a/docs/book/src/getting-started/testdata/project/config/rbac/kustomization.yaml
+++ b/docs/book/src/getting-started/testdata/project/config/rbac/kustomization.yaml
@@ -10,15 +10,15 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
# For each CRD, "Editor" and "Viewer" roles are scaffolded by
# default, aiding admins in cluster management. Those roles are
# not used by the Project itself. You can comment the following lines
# if you do not want those helpers be installed with your Project.
- memcached_editor_role.yaml
- memcached_viewer_role.yaml
+
diff --git a/docs/book/src/getting-started/testdata/project/config/rbac/auth_proxy_client_clusterrole.yaml b/docs/book/src/getting-started/testdata/project/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from docs/book/src/getting-started/testdata/project/config/rbac/auth_proxy_client_clusterrole.yaml
rename to docs/book/src/getting-started/testdata/project/config/rbac/metrics_client_cluster_role.yaml
diff --git a/docs/book/src/getting-started/testdata/project/config/rbac/auth_proxy_role.yaml b/docs/book/src/getting-started/testdata/project/config/rbac/metrics_role.yaml
similarity index 94%
rename from docs/book/src/getting-started/testdata/project/config/rbac/auth_proxy_role.yaml
rename to docs/book/src/getting-started/testdata/project/config/rbac/metrics_role.yaml
index 17e0a11d32b..2265a70613e 100644
--- a/docs/book/src/getting-started/testdata/project/config/rbac/auth_proxy_role.yaml
+++ b/docs/book/src/getting-started/testdata/project/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/auth_proxy_role_binding.yaml b/docs/book/src/getting-started/testdata/project/config/rbac/metrics_role_binding.yaml
similarity index 86%
rename from docs/book/src/cronjob-tutorial/testdata/project/config/rbac/auth_proxy_role_binding.yaml
rename to docs/book/src/getting-started/testdata/project/config/rbac/metrics_role_binding.yaml
index e1f50c3178a..e94f3a89e4c 100644
--- a/docs/book/src/cronjob-tutorial/testdata/project/config/rbac/auth_proxy_role_binding.yaml
+++ b/docs/book/src/getting-started/testdata/project/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/docs/book/src/getting-started/testdata/project/config/rbac/auth_proxy_service.yaml b/docs/book/src/getting-started/testdata/project/config/rbac/metrics_service.yaml
similarity index 100%
rename from docs/book/src/getting-started/testdata/project/config/rbac/auth_proxy_service.yaml
rename to docs/book/src/getting-started/testdata/project/config/rbac/metrics_service.yaml
diff --git a/docs/book/src/reference/metrics.md b/docs/book/src/reference/metrics.md
index 33e7e3b0a13..31c8bea5b18 100644
--- a/docs/book/src/reference/metrics.md
+++ b/docs/book/src/reference/metrics.md
@@ -3,13 +3,66 @@
By default, controller-runtime builds a global prometheus registry and
publishes [a collection of performance metrics](/reference/metrics-reference.md) for each controller.
+
+
+## Enabling the Metrics
+
+First, you will need enable the Metrics by uncommenting the following line
+in the file `config/default/kustomization.yaml`, see:
+
+```sh
+# [Metrics] The following patch will enable the metrics endpoint.
+# Ensure that you also protect this endpoint.
+#- path: manager_metrics_patch.yaml
+```
+
## Protecting the Metrics
-These metrics are protected by [kube-rbac-proxy](https://github.com/brancz/kube-rbac-proxy)
-by default if using kubebuilder. Kubebuilder v2.2.0+ scaffold a clusterrole which
-can be found at `config/rbac/auth_proxy_client_clusterrole.yaml`.
+Unprotected metrics endpoints can expose valuable data to unauthorized users,
+such as system performance, application behavior, and potentially confidential
+operational metrics. This exposure can lead to security vulnerabilities
+where an attacker could gain insights into the system's operation
+and exploit weaknesses.
+
+## RBAC Permissions for Metrics
-You will need to grant permissions to your Prometheus server so that it can
+Kubebuilder scaffold a clusterrole which
+can be found at `config/rbac/metrics_client_cluster_role.yaml`.
+
+Then, you will need to grant permissions to your Prometheus server so that it can
scrape the protected metrics. To achieve that, you can create a
`clusterRoleBinding` to bind the `clusterRole` to the service account that your
Prometheus server uses. If you are using [kube-prometheus](https://github.com/prometheus-operator/kube-prometheus),
@@ -91,6 +144,14 @@ for the metrics exported from the namespace where the project is running
 +## Consuming the Metrics from other Pods.
+
+Then, see an example to create a Pod using Curl to reach out the metrics:
+
+```sh
+kubectl run curl --restart=Never -n --image=curlimages/curl:7.78.0 -- /bin/sh -c "curl -v http://-controller-manager-metrics-service..svc.cluster.local:8080/metrics"
+```
+
## Publishing Additional Metrics
If you wish to publish additional metrics from your controllers, this
@@ -141,4 +202,4 @@ In order to publish metrics and view them on the Prometheus UI, the Prometheus i
Those metrics will be available for prometheus or
other openmetrics systems to scrape.
-
+
\ No newline at end of file
diff --git a/hack/docs/internal/cronjob-tutorial/generate_cronjob.go b/hack/docs/internal/cronjob-tutorial/generate_cronjob.go
index 97258ee47aa..3de1859c668 100644
--- a/hack/docs/internal/cronjob-tutorial/generate_cronjob.go
+++ b/hack/docs/internal/cronjob-tutorial/generate_cronjob.go
@@ -583,13 +583,6 @@ func updateExample(sp *Sample) {
filepath.Join(sp.ctx.Dir, "config/samples/batch_v1_cronjob.yaml"),
`# TODO(user): Add fields here`, "")
CheckError("fixing samples/batch_v1_cronjob.yaml", err)
-
- // update default/manager_auth_proxy_patch.yaml
- err = pluginutil.InsertCode(
- filepath.Join(sp.ctx.Dir, "config/default/manager_auth_proxy_patch.yaml"),
- ` template:
- spec:`, ManagerAuthProxySample)
- CheckError("fixing default/manager_auth_proxy_patch.yaml", err)
}
func addControllerTest(sp *Sample) {
diff --git a/hack/docs/internal/cronjob-tutorial/sample.go b/hack/docs/internal/cronjob-tutorial/sample.go
index baebb4cfa4b..7e413af1065 100644
--- a/hack/docs/internal/cronjob-tutorial/sample.go
+++ b/hack/docs/internal/cronjob-tutorial/sample.go
@@ -130,21 +130,3 @@ const DefaultKustomization = `#replacements:
# delimiter: '.'
# index: 1
# create: true`
-
-const ManagerAuthProxySample = `
- affinity:
- nodeAffinity:
- requiredDuringSchedulingIgnoredDuringExecution:
- nodeSelectorTerms:
- - matchExpressions:
- - key: kubernetes.io/arch
- operator: In
- values:
- - amd64
- - arm64
- - ppc64le
- - s390x
- - key: kubernetes.io/os
- operator: In
- values:
- - linux`
diff --git a/pkg/plugin/util/util.go b/pkg/plugin/util/util.go
index ebf5418adda..bae4e76f47f 100644
--- a/pkg/plugin/util/util.go
+++ b/pkg/plugin/util/util.go
@@ -97,6 +97,36 @@ func InsertCodeIfNotExist(filename, target, code string) error {
return InsertCode(filename, target, code)
}
+// AppendCodeIfNotExist checks if the code does not already exist in the file, and if not, appends it to the end.
+func AppendCodeIfNotExist(filename, code string) error {
+ contents, err := os.ReadFile(filename)
+ if err != nil {
+ return err
+ }
+
+ if strings.Contains(string(contents), code) {
+ return nil // Code already exists, no need to append.
+ }
+
+ return AppendCodeAtTheEnd(filename, code)
+}
+
+// AppendCodeAtTheEnd appends the given code at the end of the file.
+func AppendCodeAtTheEnd(filename, code string) error {
+ f, err := os.OpenFile(filename, os.O_APPEND|os.O_WRONLY, 0644)
+ if err != nil {
+ return err
+ }
+ defer func() {
+ if err := f.Close(); err != nil {
+ return
+ }
+ }()
+
+ _, err = f.WriteString(code)
+ return err
+}
+
// UncommentCode searches for target in the file and remove the comment prefix
// of the target content. The target content may span multiple lines.
func UncommentCode(filename, target, prefix string) error {
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/api.go b/pkg/plugins/common/kustomize/v2/scaffolds/api.go
index dc875d01235..03e3ec2b8e6 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/api.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/api.go
@@ -102,28 +102,37 @@ func (s *apiScaffolder) Scaffold() error {
// Add scaffolded CRD Editor and Viewer roles in config/rbac/kustomization.yaml
rbacKustomizeFilePath := "config/rbac/kustomization.yaml"
- comment := `
-# For each CRD, "Editor" and "Viewer" roles are scaffolded by
-# default, aiding admins in cluster management. Those roles are
-# not used by the Project itself. You can comment the following lines
-# if you do not want those helpers be installed with your Project.`
- err = pluginutil.InsertCodeIfNotExist(rbacKustomizeFilePath,
- "- auth_proxy_client_clusterrole.yaml", comment)
+ err = pluginutil.AppendCodeIfNotExist(rbacKustomizeFilePath,
+ editViewRulesCommentFragment)
if err != nil {
- log.Errorf("Unable to add a comment in the file "+
+ log.Errorf("Unable to append the edit/view roles editViewRulesCommentFragment in the file "+
"%s.", rbacKustomizeFilePath)
}
crdName := strings.ToLower(s.resource.Kind)
if s.config.IsMultiGroup() && s.resource.Group != "" {
crdName = strings.ToLower(s.resource.Group) + "_" + crdName
}
- err = pluginutil.InsertCodeIfNotExist(rbacKustomizeFilePath, comment,
+ err = pluginutil.InsertCodeIfNotExist(rbacKustomizeFilePath, editViewRulesCommentFragment,
fmt.Sprintf("\n- %[1]s_editor_role.yaml\n- %[1]s_viewer_role.yaml", crdName))
if err != nil {
log.Errorf("Unable to add Editor and Viewer roles in the file "+
"%s.", rbacKustomizeFilePath)
}
+ // Add an empty line at the end of the file
+ err = pluginutil.AppendCodeIfNotExist(rbacKustomizeFilePath,
+ `
+
+`)
+ if err != nil {
+ log.Errorf("Unable to append empty line at the end of the file"+
+ "%s.", rbacKustomizeFilePath)
+ }
}
return nil
}
+
+const editViewRulesCommentFragment = `# For each CRD, "Editor" and "Viewer" roles are scaffolded by
+# default, aiding admins in cluster management. Those roles are
+# not used by the Project itself. You can comment the following lines
+# if you do not want those helpers be installed with your Project.`
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/init.go b/pkg/plugins/common/kustomize/v2/scaffolds/init.go
index baea4bb55c6..9111e1efcfc 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/init.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/init.go
@@ -64,10 +64,10 @@ func (s *initScaffolder) Scaffold() error {
templates := []machinery.Builder{
&rbac.Kustomization{},
- &rbac.AuthProxyRole{},
- &rbac.AuthProxyRoleBinding{},
- &rbac.AuthProxyService{},
- &rbac.AuthProxyClientRole{},
+ &rbac.MetricsRole{},
+ &rbac.MonitoringBinding{},
+ &rbac.MetricsClientRole{},
+ &rbac.MetricsService{},
&rbac.RoleBinding{},
// We need to create a Role because if the project
// has not CRD define the controller-gen will not generate this file
@@ -76,9 +76,9 @@ func (s *initScaffolder) Scaffold() error {
&rbac.LeaderElectionRoleBinding{},
&rbac.ServiceAccount{},
&manager.Kustomization{},
+ &kdefault.ManagerMetricsPatch{},
&manager.Config{Image: imageName},
&kdefault.Kustomization{},
- &kdefault.ManagerAuthProxyPatch{},
&kdefault.ManagerConfigPatch{},
&prometheus.Kustomization{},
&prometheus.Monitor{},
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/enable_matrics_patch.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/enable_matrics_patch.go
new file mode 100644
index 00000000000..7a7a7e6a596
--- /dev/null
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/enable_matrics_patch.go
@@ -0,0 +1,61 @@
+/*
+Copyright 2020 The Kubernetes Authors.
+
+Licensed under the Apache License, Version 2.0 (the "License");
+you may not use this file except in compliance with the License.
+You may obtain a copy of the License at
+
+ http://www.apache.org/licenses/LICENSE-2.0
+
+Unless required by applicable law or agreed to in writing, software
+distributed under the License is distributed on an "AS IS" BASIS,
+WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+See the License for the specific language governing permissions and
+limitations under the License.
+*/
+
+package kdefault
+
+import (
+ "path/filepath"
+
+ "sigs.k8s.io/kubebuilder/v3/pkg/machinery"
+)
+
+var _ machinery.Template = &ManagerMetricsPatch{}
+
+// ManagerMetricsPatch scaffolds a file that defines the patch that enables prometheus metrics for the manager
+type ManagerMetricsPatch struct {
+ machinery.TemplateMixin
+ machinery.ComponentConfigMixin
+}
+
+// SetTemplateDefaults implements file.Template
+func (f *ManagerMetricsPatch) SetTemplateDefaults() error {
+ if f.Path == "" {
+ f.Path = filepath.Join("config", "default", "manager_metrics_patch.yaml")
+ }
+
+ f.TemplateBody = kustomizeMetricsPatchTemplate
+
+ f.IfExistsAction = machinery.Error
+
+ return nil
+}
+
+const kustomizeMetricsPatchTemplate = `# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
+`
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/kustomization.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/kustomization.go
index 319bcf1a6b3..5eccf772296 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/kustomization.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/kustomization.go
@@ -73,10 +73,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
{{ if .ComponentConfig -}}
# Mount the controller config file for loading manager configurations
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/manager_auth_proxy_patch.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/manager_auth_proxy_patch.go
deleted file mode 100644
index d8d57261952..00000000000
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/manager_auth_proxy_patch.go
+++ /dev/null
@@ -1,87 +0,0 @@
-/*
-Copyright 2020 The Kubernetes Authors.
-
-Licensed under the Apache License, Version 2.0 (the "License");
-you may not use this file except in compliance with the License.
-You may obtain a copy of the License at
-
- http://www.apache.org/licenses/LICENSE-2.0
-
-Unless required by applicable law or agreed to in writing, software
-distributed under the License is distributed on an "AS IS" BASIS,
-WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
-See the License for the specific language governing permissions and
-limitations under the License.
-*/
-
-package kdefault
-
-import (
- "path/filepath"
-
- "sigs.k8s.io/kubebuilder/v3/pkg/machinery"
-)
-
-var _ machinery.Template = &ManagerAuthProxyPatch{}
-
-// ManagerAuthProxyPatch scaffolds a file that defines the patch that enables prometheus metrics for the manager
-type ManagerAuthProxyPatch struct {
- machinery.TemplateMixin
- machinery.ComponentConfigMixin
-}
-
-// SetTemplateDefaults implements file.Template
-func (f *ManagerAuthProxyPatch) SetTemplateDefaults() error {
- if f.Path == "" {
- f.Path = filepath.Join("config", "default", "manager_auth_proxy_patch.yaml")
- }
-
- f.TemplateBody = kustomizeAuthProxyPatchTemplate
-
- f.IfExistsAction = machinery.Error
-
- return nil
-}
-
-const kustomizeAuthProxyPatchTemplate = `# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
-{{- if not .ComponentConfig }}
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
-{{- end }}
-`
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/prometheus/monitor.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/prometheus/monitor.go
index 339ca03f072..68e599044f6 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/prometheus/monitor.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/prometheus/monitor.go
@@ -58,7 +58,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/kustomization.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/kustomization.go
index d3ea9b22fd9..4133078507f 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/kustomization.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/kustomization.go
@@ -54,10 +54,9 @@ const kustomizeRBACTemplate = `resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
`
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_client_role.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_client_role.go
similarity index 70%
rename from pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_client_role.go
rename to pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_client_role.go
index a348524ab4a..c178ab71ce7 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_client_role.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_client_role.go
@@ -22,26 +22,26 @@ import (
"sigs.k8s.io/kubebuilder/v3/pkg/machinery"
)
-var _ machinery.Template = &AuthProxyClientRole{}
+var _ machinery.Template = &MetricsClientRole{}
-// AuthProxyClientRole scaffolds a file that defines the role for the metrics reader
-type AuthProxyClientRole struct {
+// MetricsClientRole scaffolds a file that defines the role for the metrics reader
+type MetricsClientRole struct {
machinery.TemplateMixin
machinery.ProjectNameMixin
}
// SetTemplateDefaults implements file.Template
-func (f *AuthProxyClientRole) SetTemplateDefaults() error {
+func (f *MetricsClientRole) SetTemplateDefaults() error {
if f.Path == "" {
- f.Path = filepath.Join("config", "rbac", "auth_proxy_client_clusterrole.yaml")
+ f.Path = filepath.Join("config", "rbac", "metrics_client_cluster_role.yaml")
}
- f.TemplateBody = clientClusterRoleTemplate
+ f.TemplateBody = metricsClientClusterRoleTemplate
return nil
}
-const clientClusterRoleTemplate = `apiVersion: rbac.authorization.k8s.io/v1
+const metricsClientClusterRoleTemplate = `apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_role.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_role.go
similarity index 74%
rename from pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_role.go
rename to pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_role.go
index d1b639c0ee3..f45a39855d2 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_role.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_role.go
@@ -22,32 +22,32 @@ import (
"sigs.k8s.io/kubebuilder/v3/pkg/machinery"
)
-var _ machinery.Template = &AuthProxyRole{}
+var _ machinery.Template = &MetricsRole{}
-// AuthProxyRole scaffolds a file that defines the role for the auth proxy
-type AuthProxyRole struct {
+// MetricsRole scaffolds a file that defines the role for the auth proxy
+type MetricsRole struct {
machinery.TemplateMixin
machinery.ProjectNameMixin
}
// SetTemplateDefaults implements file.Template
-func (f *AuthProxyRole) SetTemplateDefaults() error {
+func (f *MetricsRole) SetTemplateDefaults() error {
if f.Path == "" {
- f.Path = filepath.Join("config", "rbac", "auth_proxy_role.yaml")
+ f.Path = filepath.Join("config", "rbac", "metrics_role.yaml")
}
- f.TemplateBody = proxyRoleTemplate
+ f.TemplateBody = metricsRoleTemplate
return nil
}
-const proxyRoleTemplate = `apiVersion: rbac.authorization.k8s.io/v1
+const metricsRoleTemplate = `apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/name: {{ .ProjectName }}
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_role_binding.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_role_binding.go
similarity index 69%
rename from pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_role_binding.go
rename to pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_role_binding.go
index 4ee86ed5c0f..9ea74c8679f 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_role_binding.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_role_binding.go
@@ -22,36 +22,36 @@ import (
"sigs.k8s.io/kubebuilder/v3/pkg/machinery"
)
-var _ machinery.Template = &AuthProxyRoleBinding{}
+var _ machinery.Template = &MonitoringBinding{}
-// AuthProxyRoleBinding scaffolds a file that defines the role binding for the auth proxy
-type AuthProxyRoleBinding struct {
+// MonitoringBinding scaffolds a file that defines the role binding for the auth proxy
+type MonitoringBinding struct {
machinery.TemplateMixin
machinery.ProjectNameMixin
}
// SetTemplateDefaults implements file.Template
-func (f *AuthProxyRoleBinding) SetTemplateDefaults() error {
+func (f *MonitoringBinding) SetTemplateDefaults() error {
if f.Path == "" {
- f.Path = filepath.Join("config", "rbac", "auth_proxy_role_binding.yaml")
+ f.Path = filepath.Join("config", "rbac", "metrics_role_binding.yaml")
}
- f.TemplateBody = proxyRoleBindinggTemplate
+ f.TemplateBody = metricsRoleBindinggTemplate
return nil
}
-const proxyRoleBindinggTemplate = `apiVersion: rbac.authorization.k8s.io/v1
+const metricsRoleBindinggTemplate = `apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/name: {{ .ProjectName }}
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_service.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_service.go
similarity index 75%
rename from pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_service.go
rename to pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_service.go
index 219efc86ed7..c5e5da558ed 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_service.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_service.go
@@ -22,26 +22,26 @@ import (
"sigs.k8s.io/kubebuilder/v3/pkg/machinery"
)
-var _ machinery.Template = &AuthProxyService{}
+var _ machinery.Template = &MetricsService{}
-// AuthProxyService scaffolds a file that defines the service for the auth proxy
-type AuthProxyService struct {
+// MetricsService scaffolds a file that defines the service for the auth proxy
+type MetricsService struct {
machinery.TemplateMixin
machinery.ProjectNameMixin
}
// SetTemplateDefaults implements file.Template
-func (f *AuthProxyService) SetTemplateDefaults() error {
+func (f *MetricsService) SetTemplateDefaults() error {
if f.Path == "" {
- f.Path = filepath.Join("config", "rbac", "auth_proxy_service.yaml")
+ f.Path = filepath.Join("config", "rbac", "metrics_service.yaml")
}
- f.TemplateBody = authProxyServiceTemplate
+ f.TemplateBody = metricsServiceTemplate
return nil
}
-const authProxyServiceTemplate = `apiVersion: v1
+const metricsServiceTemplate = `apiVersion: v1
kind: Service
metadata:
labels:
diff --git a/test/e2e/v4/generate_test.go b/test/e2e/v4/generate_test.go
index 02f72b01910..9a8155ca84d 100644
--- a/test/e2e/v4/generate_test.go
+++ b/test/e2e/v4/generate_test.go
@@ -63,6 +63,10 @@ func GenerateV4(kbc *utils.TestContext) {
ExpectWithOffset(1, pluginutil.UncommentCode(
filepath.Join(kbc.Dir, "config", "default", "kustomization.yaml"),
"#- path: webhookcainjection_patch.yaml", "#")).To(Succeed())
+ ExpectWithOffset(1, pluginutil.UncommentCode(
+ filepath.Join(kbc.Dir, "config", "default", "kustomization.yaml"),
+ "#- path: manager_metrics_patch.yaml", "#")).To(Succeed())
+
ExpectWithOffset(1, pluginutil.UncommentCode(filepath.Join(kbc.Dir, "config", "default", "kustomization.yaml"),
certManagerTarget, "#")).To(Succeed())
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/default/kustomization.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/default/kustomization.yaml
index 2f78dfb54aa..b5f4c2a79b6 100644
--- a/testdata/project-v4-multigroup-with-deploy-image/config/default/kustomization.yaml
+++ b/testdata/project-v4-multigroup-with-deploy-image/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# [WEBHOOK] To enable webhook, uncomment all the sections with [WEBHOOK] prefix including the one in
# crd/kustomization.yaml
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/default/manager_auth_proxy_patch.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 4c3c27602f5..00000000000
--- a/testdata/project-v4-multigroup-with-deploy-image/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,39 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/default/manager_metrics_patch.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/testdata/project-v4-multigroup-with-deploy-image/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/prometheus/monitor.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/prometheus/monitor.yaml
index c7e880652bc..68b33ecd8b5 100644
--- a/testdata/project-v4-multigroup-with-deploy-image/config/prometheus/monitor.yaml
+++ b/testdata/project-v4-multigroup-with-deploy-image/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/kustomization.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/kustomization.yaml
index 08b359e46b5..5dc6fddec28 100644
--- a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/kustomization.yaml
+++ b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/kustomization.yaml
@@ -10,12 +10,11 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
# For each CRD, "Editor" and "Viewer" roles are scaffolded by
# default, aiding admins in cluster management. Those roles are
# not used by the Project itself. You can comment the following lines
@@ -40,3 +39,4 @@ resources:
- ship_frigate_viewer_role.yaml
- crew_captain_editor_role.yaml
- crew_captain_viewer_role.yaml
+
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_client_clusterrole.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_client_clusterrole.yaml
rename to testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_client_cluster_role.yaml
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_role.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_role.yaml
similarity index 94%
rename from testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_role.yaml
rename to testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_role.yaml
index 13038ff7689..82404922028 100644
--- a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_role.yaml
+++ b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-multigroup-with-deploy-image
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_role_binding.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_role_binding.yaml
similarity index 87%
rename from testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_role_binding.yaml
rename to testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_role_binding.yaml
index aae73208a49..e90cead25f4 100644
--- a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_role_binding.yaml
+++ b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-multigroup-with-deploy-image
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_service.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_service.yaml
similarity index 100%
rename from testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_service.yaml
rename to testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_service.yaml
diff --git a/testdata/project-v4-multigroup-with-deploy-image/dist/install.yaml b/testdata/project-v4-multigroup-with-deploy-image/dist/install.yaml
index 26592d65d9a..46b43298a67 100644
--- a/testdata/project-v4-multigroup-with-deploy-image/dist/install.yaml
+++ b/testdata/project-v4-multigroup-with-deploy-image/dist/install.yaml
@@ -1208,7 +1208,7 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-multigroup-with-deploy-image
- name: project-v4-multigroup-with-deploy-image-proxy-role
+ name: project-v4-multigroup-with-deploy-image-metrics-role
rules:
- apiGroups:
- authentication.k8s.io
@@ -1512,11 +1512,11 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-multigroup-with-deploy-image
- name: project-v4-multigroup-with-deploy-image-proxy-rolebinding
+ name: project-v4-multigroup-with-deploy-image-metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: project-v4-multigroup-with-deploy-image-proxy-role
+ name: project-v4-multigroup-with-deploy-image-metrics-role
subjects:
- kind: ServiceAccount
name: project-v4-multigroup-with-deploy-image-controller-manager
@@ -1579,8 +1579,6 @@ spec:
spec:
containers:
- args:
- - --health-probe-bind-address=:8081
- - --metrics-bind-address=127.0.0.1:8080
- --leader-elect
command:
- /manager
@@ -1618,29 +1616,6 @@ spec:
- mountPath: /tmp/k8s-webhook-server/serving-certs
name: cert
readOnly: true
- - args:
- - --secure-listen-address=0.0.0.0:8443
- - --upstream=http://127.0.0.1:8080/
- - --logtostderr=true
- - --v=0
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- name: kube-rbac-proxy
- ports:
- - containerPort: 8443
- name: https
- protocol: TCP
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - ALL
securityContext:
runAsNonRoot: true
serviceAccountName: project-v4-multigroup-with-deploy-image-controller-manager
diff --git a/testdata/project-v4-multigroup/config/default/kustomization.yaml b/testdata/project-v4-multigroup/config/default/kustomization.yaml
index 9fe6e3630df..ac074b25f9c 100644
--- a/testdata/project-v4-multigroup/config/default/kustomization.yaml
+++ b/testdata/project-v4-multigroup/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# [WEBHOOK] To enable webhook, uncomment all the sections with [WEBHOOK] prefix including the one in
# crd/kustomization.yaml
diff --git a/testdata/project-v4-multigroup/config/default/manager_auth_proxy_patch.yaml b/testdata/project-v4-multigroup/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 4c3c27602f5..00000000000
--- a/testdata/project-v4-multigroup/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,39 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
diff --git a/testdata/project-v4-multigroup/config/default/manager_metrics_patch.yaml b/testdata/project-v4-multigroup/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/testdata/project-v4-multigroup/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/testdata/project-v4-multigroup/config/prometheus/monitor.yaml b/testdata/project-v4-multigroup/config/prometheus/monitor.yaml
index bb60c0d334a..443f65de517 100644
--- a/testdata/project-v4-multigroup/config/prometheus/monitor.yaml
+++ b/testdata/project-v4-multigroup/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/testdata/project-v4-multigroup/config/rbac/kustomization.yaml b/testdata/project-v4-multigroup/config/rbac/kustomization.yaml
index 08b359e46b5..5dc6fddec28 100644
--- a/testdata/project-v4-multigroup/config/rbac/kustomization.yaml
+++ b/testdata/project-v4-multigroup/config/rbac/kustomization.yaml
@@ -10,12 +10,11 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
# For each CRD, "Editor" and "Viewer" roles are scaffolded by
# default, aiding admins in cluster management. Those roles are
# not used by the Project itself. You can comment the following lines
@@ -40,3 +39,4 @@ resources:
- ship_frigate_viewer_role.yaml
- crew_captain_editor_role.yaml
- crew_captain_viewer_role.yaml
+
diff --git a/testdata/project-v4-multigroup/config/rbac/auth_proxy_client_clusterrole.yaml b/testdata/project-v4-multigroup/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from testdata/project-v4-multigroup/config/rbac/auth_proxy_client_clusterrole.yaml
rename to testdata/project-v4-multigroup/config/rbac/metrics_client_cluster_role.yaml
diff --git a/testdata/project-v4-multigroup/config/rbac/auth_proxy_role.yaml b/testdata/project-v4-multigroup/config/rbac/metrics_role.yaml
similarity index 94%
rename from testdata/project-v4-multigroup/config/rbac/auth_proxy_role.yaml
rename to testdata/project-v4-multigroup/config/rbac/metrics_role.yaml
index 56c97ddca82..a7b19928c33 100644
--- a/testdata/project-v4-multigroup/config/rbac/auth_proxy_role.yaml
+++ b/testdata/project-v4-multigroup/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-multigroup
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/testdata/project-v4-multigroup/config/rbac/auth_proxy_role_binding.yaml b/testdata/project-v4-multigroup/config/rbac/metrics_role_binding.yaml
similarity index 86%
rename from testdata/project-v4-multigroup/config/rbac/auth_proxy_role_binding.yaml
rename to testdata/project-v4-multigroup/config/rbac/metrics_role_binding.yaml
index 10f89301cdb..3af6d2f11cc 100644
--- a/testdata/project-v4-multigroup/config/rbac/auth_proxy_role_binding.yaml
+++ b/testdata/project-v4-multigroup/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-multigroup
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/testdata/project-v4-multigroup/config/rbac/auth_proxy_service.yaml b/testdata/project-v4-multigroup/config/rbac/metrics_service.yaml
similarity index 100%
rename from testdata/project-v4-multigroup/config/rbac/auth_proxy_service.yaml
rename to testdata/project-v4-multigroup/config/rbac/metrics_service.yaml
diff --git a/testdata/project-v4-multigroup/dist/install.yaml b/testdata/project-v4-multigroup/dist/install.yaml
index e2584bdeac2..e0331e1d27f 100644
--- a/testdata/project-v4-multigroup/dist/install.yaml
+++ b/testdata/project-v4-multigroup/dist/install.yaml
@@ -1208,7 +1208,7 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-multigroup
- name: project-v4-multigroup-proxy-role
+ name: project-v4-multigroup-metrics-role
rules:
- apiGroups:
- authentication.k8s.io
@@ -1512,11 +1512,11 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-multigroup
- name: project-v4-multigroup-proxy-rolebinding
+ name: project-v4-multigroup-metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: project-v4-multigroup-proxy-role
+ name: project-v4-multigroup-metrics-role
subjects:
- kind: ServiceAccount
name: project-v4-multigroup-controller-manager
@@ -1579,8 +1579,6 @@ spec:
spec:
containers:
- args:
- - --health-probe-bind-address=:8081
- - --metrics-bind-address=127.0.0.1:8080
- --leader-elect
command:
- /manager
@@ -1618,29 +1616,6 @@ spec:
- mountPath: /tmp/k8s-webhook-server/serving-certs
name: cert
readOnly: true
- - args:
- - --secure-listen-address=0.0.0.0:8443
- - --upstream=http://127.0.0.1:8080/
- - --logtostderr=true
- - --v=0
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- name: kube-rbac-proxy
- ports:
- - containerPort: 8443
- name: https
- protocol: TCP
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - ALL
securityContext:
runAsNonRoot: true
serviceAccountName: project-v4-multigroup-controller-manager
diff --git a/testdata/project-v4-with-deploy-image/config/default/kustomization.yaml b/testdata/project-v4-with-deploy-image/config/default/kustomization.yaml
index 62e78ccdbbe..a81c828747b 100644
--- a/testdata/project-v4-with-deploy-image/config/default/kustomization.yaml
+++ b/testdata/project-v4-with-deploy-image/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# [WEBHOOK] To enable webhook, uncomment all the sections with [WEBHOOK] prefix including the one in
# crd/kustomization.yaml
diff --git a/testdata/project-v4-with-deploy-image/config/default/manager_auth_proxy_patch.yaml b/testdata/project-v4-with-deploy-image/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 4c3c27602f5..00000000000
--- a/testdata/project-v4-with-deploy-image/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,39 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
diff --git a/testdata/project-v4-with-deploy-image/config/default/manager_metrics_patch.yaml b/testdata/project-v4-with-deploy-image/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/testdata/project-v4-with-deploy-image/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/testdata/project-v4-with-deploy-image/config/prometheus/monitor.yaml b/testdata/project-v4-with-deploy-image/config/prometheus/monitor.yaml
index 0f805f2c2e7..51baef4b2e0 100644
--- a/testdata/project-v4-with-deploy-image/config/prometheus/monitor.yaml
+++ b/testdata/project-v4-with-deploy-image/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/testdata/project-v4-with-deploy-image/config/rbac/kustomization.yaml b/testdata/project-v4-with-deploy-image/config/rbac/kustomization.yaml
index 67076dab990..3f08cb60620 100644
--- a/testdata/project-v4-with-deploy-image/config/rbac/kustomization.yaml
+++ b/testdata/project-v4-with-deploy-image/config/rbac/kustomization.yaml
@@ -10,12 +10,11 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
# For each CRD, "Editor" and "Viewer" roles are scaffolded by
# default, aiding admins in cluster management. Those roles are
# not used by the Project itself. You can comment the following lines
@@ -24,3 +23,4 @@ resources:
- busybox_viewer_role.yaml
- memcached_editor_role.yaml
- memcached_viewer_role.yaml
+
diff --git a/testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_client_clusterrole.yaml b/testdata/project-v4-with-deploy-image/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_client_clusterrole.yaml
rename to testdata/project-v4-with-deploy-image/config/rbac/metrics_client_cluster_role.yaml
diff --git a/testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_role.yaml b/testdata/project-v4-with-deploy-image/config/rbac/metrics_role.yaml
similarity index 94%
rename from testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_role.yaml
rename to testdata/project-v4-with-deploy-image/config/rbac/metrics_role.yaml
index 438d9bd0702..690aba51194 100644
--- a/testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_role.yaml
+++ b/testdata/project-v4-with-deploy-image/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-with-deploy-image
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_role_binding.yaml b/testdata/project-v4-with-deploy-image/config/rbac/metrics_role_binding.yaml
similarity index 87%
rename from testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_role_binding.yaml
rename to testdata/project-v4-with-deploy-image/config/rbac/metrics_role_binding.yaml
index 3be0002395d..caba0e4981c 100644
--- a/testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_role_binding.yaml
+++ b/testdata/project-v4-with-deploy-image/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-with-deploy-image
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_service.yaml b/testdata/project-v4-with-deploy-image/config/rbac/metrics_service.yaml
similarity index 100%
rename from testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_service.yaml
rename to testdata/project-v4-with-deploy-image/config/rbac/metrics_service.yaml
diff --git a/testdata/project-v4-with-deploy-image/dist/install.yaml b/testdata/project-v4-with-deploy-image/dist/install.yaml
index 70babe98cbe..8a820153db9 100644
--- a/testdata/project-v4-with-deploy-image/dist/install.yaml
+++ b/testdata/project-v4-with-deploy-image/dist/install.yaml
@@ -534,7 +534,7 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-with-deploy-image
- name: project-v4-with-deploy-image-proxy-role
+ name: project-v4-with-deploy-image-metrics-role
rules:
- apiGroups:
- authentication.k8s.io
@@ -588,11 +588,11 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-with-deploy-image
- name: project-v4-with-deploy-image-proxy-rolebinding
+ name: project-v4-with-deploy-image-metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: project-v4-with-deploy-image-proxy-role
+ name: project-v4-with-deploy-image-metrics-role
subjects:
- kind: ServiceAccount
name: project-v4-with-deploy-image-controller-manager
@@ -655,8 +655,6 @@ spec:
spec:
containers:
- args:
- - --health-probe-bind-address=:8081
- - --metrics-bind-address=127.0.0.1:8080
- --leader-elect
command:
- /manager
@@ -699,29 +697,6 @@ spec:
- mountPath: /tmp/k8s-webhook-server/serving-certs
name: cert
readOnly: true
- - args:
- - --secure-listen-address=0.0.0.0:8443
- - --upstream=http://127.0.0.1:8080/
- - --logtostderr=true
- - --v=0
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- name: kube-rbac-proxy
- ports:
- - containerPort: 8443
- name: https
- protocol: TCP
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - ALL
securityContext:
runAsNonRoot: true
serviceAccountName: project-v4-with-deploy-image-controller-manager
diff --git a/testdata/project-v4-with-grafana/config/default/kustomization.yaml b/testdata/project-v4-with-grafana/config/default/kustomization.yaml
index 7fca0820b0c..b6daeb7047d 100644
--- a/testdata/project-v4-with-grafana/config/default/kustomization.yaml
+++ b/testdata/project-v4-with-grafana/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# [WEBHOOK] To enable webhook, uncomment all the sections with [WEBHOOK] prefix including the one in
# crd/kustomization.yaml
diff --git a/testdata/project-v4-with-grafana/config/default/manager_auth_proxy_patch.yaml b/testdata/project-v4-with-grafana/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 4c3c27602f5..00000000000
--- a/testdata/project-v4-with-grafana/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,39 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
diff --git a/testdata/project-v4-with-grafana/config/default/manager_metrics_patch.yaml b/testdata/project-v4-with-grafana/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/testdata/project-v4-with-grafana/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/testdata/project-v4-with-grafana/config/prometheus/monitor.yaml b/testdata/project-v4-with-grafana/config/prometheus/monitor.yaml
index 8505bfa5bfc..47e4734ad4d 100644
--- a/testdata/project-v4-with-grafana/config/prometheus/monitor.yaml
+++ b/testdata/project-v4-with-grafana/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/testdata/project-v4-with-grafana/config/rbac/kustomization.yaml b/testdata/project-v4-with-grafana/config/rbac/kustomization.yaml
index 731832a6ac3..9109783ed39 100644
--- a/testdata/project-v4-with-grafana/config/rbac/kustomization.yaml
+++ b/testdata/project-v4-with-grafana/config/rbac/kustomization.yaml
@@ -10,9 +10,8 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
diff --git a/testdata/project-v4-with-grafana/config/rbac/auth_proxy_client_clusterrole.yaml b/testdata/project-v4-with-grafana/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from testdata/project-v4-with-grafana/config/rbac/auth_proxy_client_clusterrole.yaml
rename to testdata/project-v4-with-grafana/config/rbac/metrics_client_cluster_role.yaml
diff --git a/testdata/project-v4-with-grafana/config/rbac/auth_proxy_role.yaml b/testdata/project-v4-with-grafana/config/rbac/metrics_role.yaml
similarity index 94%
rename from testdata/project-v4-with-grafana/config/rbac/auth_proxy_role.yaml
rename to testdata/project-v4-with-grafana/config/rbac/metrics_role.yaml
index 979bc272f7a..44a25d5fb06 100644
--- a/testdata/project-v4-with-grafana/config/rbac/auth_proxy_role.yaml
+++ b/testdata/project-v4-with-grafana/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-with-grafana
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/testdata/project-v4-with-grafana/config/rbac/auth_proxy_role_binding.yaml b/testdata/project-v4-with-grafana/config/rbac/metrics_role_binding.yaml
similarity index 87%
rename from testdata/project-v4-with-grafana/config/rbac/auth_proxy_role_binding.yaml
rename to testdata/project-v4-with-grafana/config/rbac/metrics_role_binding.yaml
index b5302ea3805..cd500e72cf2 100644
--- a/testdata/project-v4-with-grafana/config/rbac/auth_proxy_role_binding.yaml
+++ b/testdata/project-v4-with-grafana/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-with-grafana
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/testdata/project-v4-with-grafana/config/rbac/auth_proxy_service.yaml b/testdata/project-v4-with-grafana/config/rbac/metrics_service.yaml
similarity index 100%
rename from testdata/project-v4-with-grafana/config/rbac/auth_proxy_service.yaml
rename to testdata/project-v4-with-grafana/config/rbac/metrics_service.yaml
diff --git a/testdata/project-v4-with-grafana/dist/install.yaml b/testdata/project-v4-with-grafana/dist/install.yaml
index 5877a647805..f832955adc9 100644
--- a/testdata/project-v4-with-grafana/dist/install.yaml
+++ b/testdata/project-v4-with-grafana/dist/install.yaml
@@ -93,7 +93,7 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-with-grafana
- name: project-v4-with-grafana-proxy-role
+ name: project-v4-with-grafana-metrics-role
rules:
- apiGroups:
- authentication.k8s.io
@@ -147,11 +147,11 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-with-grafana
- name: project-v4-with-grafana-proxy-rolebinding
+ name: project-v4-with-grafana-metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: project-v4-with-grafana-proxy-role
+ name: project-v4-with-grafana-metrics-role
subjects:
- kind: ServiceAccount
name: project-v4-with-grafana-controller-manager
@@ -198,31 +198,6 @@ spec:
spec:
containers:
- args:
- - --secure-listen-address=0.0.0.0:8443
- - --upstream=http://127.0.0.1:8080/
- - --logtostderr=true
- - --v=0
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- name: kube-rbac-proxy
- ports:
- - containerPort: 8443
- name: https
- protocol: TCP
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - ALL
- - args:
- - --health-probe-bind-address=:8081
- - --metrics-bind-address=127.0.0.1:8080
- --leader-elect
command:
- /manager
diff --git a/testdata/project-v4/config/default/kustomization.yaml b/testdata/project-v4/config/default/kustomization.yaml
index ae7fc170730..45e22d821f0 100644
--- a/testdata/project-v4/config/default/kustomization.yaml
+++ b/testdata/project-v4/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# [WEBHOOK] To enable webhook, uncomment all the sections with [WEBHOOK] prefix including the one in
# crd/kustomization.yaml
diff --git a/testdata/project-v4/config/default/manager_auth_proxy_patch.yaml b/testdata/project-v4/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 4c3c27602f5..00000000000
--- a/testdata/project-v4/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,39 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
diff --git a/testdata/project-v4/config/default/manager_metrics_patch.yaml b/testdata/project-v4/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/testdata/project-v4/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/testdata/project-v4/config/prometheus/monitor.yaml b/testdata/project-v4/config/prometheus/monitor.yaml
index 767555588d4..508a47f266c 100644
--- a/testdata/project-v4/config/prometheus/monitor.yaml
+++ b/testdata/project-v4/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/testdata/project-v4/config/rbac/kustomization.yaml b/testdata/project-v4/config/rbac/kustomization.yaml
index 8518bf9e24d..59b33241e4c 100644
--- a/testdata/project-v4/config/rbac/kustomization.yaml
+++ b/testdata/project-v4/config/rbac/kustomization.yaml
@@ -10,12 +10,11 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
# For each CRD, "Editor" and "Viewer" roles are scaffolded by
# default, aiding admins in cluster management. Those roles are
# not used by the Project itself. You can comment the following lines
@@ -26,3 +25,4 @@ resources:
- firstmate_viewer_role.yaml
- captain_editor_role.yaml
- captain_viewer_role.yaml
+
diff --git a/testdata/project-v4/config/rbac/auth_proxy_client_clusterrole.yaml b/testdata/project-v4/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from testdata/project-v4/config/rbac/auth_proxy_client_clusterrole.yaml
rename to testdata/project-v4/config/rbac/metrics_client_cluster_role.yaml
diff --git a/testdata/project-v4/config/rbac/auth_proxy_role.yaml b/testdata/project-v4/config/rbac/metrics_role.yaml
similarity index 94%
rename from testdata/project-v4/config/rbac/auth_proxy_role.yaml
rename to testdata/project-v4/config/rbac/metrics_role.yaml
index 43aa96480ad..22183eb2b2e 100644
--- a/testdata/project-v4/config/rbac/auth_proxy_role.yaml
+++ b/testdata/project-v4/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project-v4
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/testdata/project-v4/config/rbac/auth_proxy_role_binding.yaml b/testdata/project-v4/config/rbac/metrics_role_binding.yaml
similarity index 86%
rename from testdata/project-v4/config/rbac/auth_proxy_role_binding.yaml
rename to testdata/project-v4/config/rbac/metrics_role_binding.yaml
index e5bbe0214cd..a5d55acfa29 100644
--- a/testdata/project-v4/config/rbac/auth_proxy_role_binding.yaml
+++ b/testdata/project-v4/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project-v4
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/testdata/project-v4/config/rbac/auth_proxy_service.yaml b/testdata/project-v4/config/rbac/metrics_service.yaml
similarity index 100%
rename from testdata/project-v4/config/rbac/auth_proxy_service.yaml
rename to testdata/project-v4/config/rbac/metrics_service.yaml
diff --git a/testdata/project-v4/dist/install.yaml b/testdata/project-v4/dist/install.yaml
index 4466171f902..5601a85da95 100644
--- a/testdata/project-v4/dist/install.yaml
+++ b/testdata/project-v4/dist/install.yaml
@@ -528,7 +528,7 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4
- name: project-v4-proxy-role
+ name: project-v4-metrics-role
rules:
- apiGroups:
- authentication.k8s.io
@@ -582,11 +582,11 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4
- name: project-v4-proxy-rolebinding
+ name: project-v4-metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: project-v4-proxy-role
+ name: project-v4-metrics-role
subjects:
- kind: ServiceAccount
name: project-v4-controller-manager
@@ -649,8 +649,6 @@ spec:
spec:
containers:
- args:
- - --health-probe-bind-address=:8081
- - --metrics-bind-address=127.0.0.1:8080
- --leader-elect
command:
- /manager
@@ -688,29 +686,6 @@ spec:
- mountPath: /tmp/k8s-webhook-server/serving-certs
name: cert
readOnly: true
- - args:
- - --secure-listen-address=0.0.0.0:8443
- - --upstream=http://127.0.0.1:8080/
- - --logtostderr=true
- - --v=0
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- name: kube-rbac-proxy
- ports:
- - containerPort: 8443
- name: https
- protocol: TCP
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - ALL
securityContext:
runAsNonRoot: true
serviceAccountName: project-v4-controller-manager
+## Consuming the Metrics from other Pods.
+
+Then, see an example to create a Pod using Curl to reach out the metrics:
+
+```sh
+kubectl run curl --restart=Never -n --image=curlimages/curl:7.78.0 -- /bin/sh -c "curl -v http://-controller-manager-metrics-service..svc.cluster.local:8080/metrics"
+```
+
## Publishing Additional Metrics
If you wish to publish additional metrics from your controllers, this
@@ -141,4 +202,4 @@ In order to publish metrics and view them on the Prometheus UI, the Prometheus i
Those metrics will be available for prometheus or
other openmetrics systems to scrape.
-
+
\ No newline at end of file
diff --git a/hack/docs/internal/cronjob-tutorial/generate_cronjob.go b/hack/docs/internal/cronjob-tutorial/generate_cronjob.go
index 97258ee47aa..3de1859c668 100644
--- a/hack/docs/internal/cronjob-tutorial/generate_cronjob.go
+++ b/hack/docs/internal/cronjob-tutorial/generate_cronjob.go
@@ -583,13 +583,6 @@ func updateExample(sp *Sample) {
filepath.Join(sp.ctx.Dir, "config/samples/batch_v1_cronjob.yaml"),
`# TODO(user): Add fields here`, "")
CheckError("fixing samples/batch_v1_cronjob.yaml", err)
-
- // update default/manager_auth_proxy_patch.yaml
- err = pluginutil.InsertCode(
- filepath.Join(sp.ctx.Dir, "config/default/manager_auth_proxy_patch.yaml"),
- ` template:
- spec:`, ManagerAuthProxySample)
- CheckError("fixing default/manager_auth_proxy_patch.yaml", err)
}
func addControllerTest(sp *Sample) {
diff --git a/hack/docs/internal/cronjob-tutorial/sample.go b/hack/docs/internal/cronjob-tutorial/sample.go
index baebb4cfa4b..7e413af1065 100644
--- a/hack/docs/internal/cronjob-tutorial/sample.go
+++ b/hack/docs/internal/cronjob-tutorial/sample.go
@@ -130,21 +130,3 @@ const DefaultKustomization = `#replacements:
# delimiter: '.'
# index: 1
# create: true`
-
-const ManagerAuthProxySample = `
- affinity:
- nodeAffinity:
- requiredDuringSchedulingIgnoredDuringExecution:
- nodeSelectorTerms:
- - matchExpressions:
- - key: kubernetes.io/arch
- operator: In
- values:
- - amd64
- - arm64
- - ppc64le
- - s390x
- - key: kubernetes.io/os
- operator: In
- values:
- - linux`
diff --git a/pkg/plugin/util/util.go b/pkg/plugin/util/util.go
index ebf5418adda..bae4e76f47f 100644
--- a/pkg/plugin/util/util.go
+++ b/pkg/plugin/util/util.go
@@ -97,6 +97,36 @@ func InsertCodeIfNotExist(filename, target, code string) error {
return InsertCode(filename, target, code)
}
+// AppendCodeIfNotExist checks if the code does not already exist in the file, and if not, appends it to the end.
+func AppendCodeIfNotExist(filename, code string) error {
+ contents, err := os.ReadFile(filename)
+ if err != nil {
+ return err
+ }
+
+ if strings.Contains(string(contents), code) {
+ return nil // Code already exists, no need to append.
+ }
+
+ return AppendCodeAtTheEnd(filename, code)
+}
+
+// AppendCodeAtTheEnd appends the given code at the end of the file.
+func AppendCodeAtTheEnd(filename, code string) error {
+ f, err := os.OpenFile(filename, os.O_APPEND|os.O_WRONLY, 0644)
+ if err != nil {
+ return err
+ }
+ defer func() {
+ if err := f.Close(); err != nil {
+ return
+ }
+ }()
+
+ _, err = f.WriteString(code)
+ return err
+}
+
// UncommentCode searches for target in the file and remove the comment prefix
// of the target content. The target content may span multiple lines.
func UncommentCode(filename, target, prefix string) error {
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/api.go b/pkg/plugins/common/kustomize/v2/scaffolds/api.go
index dc875d01235..03e3ec2b8e6 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/api.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/api.go
@@ -102,28 +102,37 @@ func (s *apiScaffolder) Scaffold() error {
// Add scaffolded CRD Editor and Viewer roles in config/rbac/kustomization.yaml
rbacKustomizeFilePath := "config/rbac/kustomization.yaml"
- comment := `
-# For each CRD, "Editor" and "Viewer" roles are scaffolded by
-# default, aiding admins in cluster management. Those roles are
-# not used by the Project itself. You can comment the following lines
-# if you do not want those helpers be installed with your Project.`
- err = pluginutil.InsertCodeIfNotExist(rbacKustomizeFilePath,
- "- auth_proxy_client_clusterrole.yaml", comment)
+ err = pluginutil.AppendCodeIfNotExist(rbacKustomizeFilePath,
+ editViewRulesCommentFragment)
if err != nil {
- log.Errorf("Unable to add a comment in the file "+
+ log.Errorf("Unable to append the edit/view roles editViewRulesCommentFragment in the file "+
"%s.", rbacKustomizeFilePath)
}
crdName := strings.ToLower(s.resource.Kind)
if s.config.IsMultiGroup() && s.resource.Group != "" {
crdName = strings.ToLower(s.resource.Group) + "_" + crdName
}
- err = pluginutil.InsertCodeIfNotExist(rbacKustomizeFilePath, comment,
+ err = pluginutil.InsertCodeIfNotExist(rbacKustomizeFilePath, editViewRulesCommentFragment,
fmt.Sprintf("\n- %[1]s_editor_role.yaml\n- %[1]s_viewer_role.yaml", crdName))
if err != nil {
log.Errorf("Unable to add Editor and Viewer roles in the file "+
"%s.", rbacKustomizeFilePath)
}
+ // Add an empty line at the end of the file
+ err = pluginutil.AppendCodeIfNotExist(rbacKustomizeFilePath,
+ `
+
+`)
+ if err != nil {
+ log.Errorf("Unable to append empty line at the end of the file"+
+ "%s.", rbacKustomizeFilePath)
+ }
}
return nil
}
+
+const editViewRulesCommentFragment = `# For each CRD, "Editor" and "Viewer" roles are scaffolded by
+# default, aiding admins in cluster management. Those roles are
+# not used by the Project itself. You can comment the following lines
+# if you do not want those helpers be installed with your Project.`
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/init.go b/pkg/plugins/common/kustomize/v2/scaffolds/init.go
index baea4bb55c6..9111e1efcfc 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/init.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/init.go
@@ -64,10 +64,10 @@ func (s *initScaffolder) Scaffold() error {
templates := []machinery.Builder{
&rbac.Kustomization{},
- &rbac.AuthProxyRole{},
- &rbac.AuthProxyRoleBinding{},
- &rbac.AuthProxyService{},
- &rbac.AuthProxyClientRole{},
+ &rbac.MetricsRole{},
+ &rbac.MonitoringBinding{},
+ &rbac.MetricsClientRole{},
+ &rbac.MetricsService{},
&rbac.RoleBinding{},
// We need to create a Role because if the project
// has not CRD define the controller-gen will not generate this file
@@ -76,9 +76,9 @@ func (s *initScaffolder) Scaffold() error {
&rbac.LeaderElectionRoleBinding{},
&rbac.ServiceAccount{},
&manager.Kustomization{},
+ &kdefault.ManagerMetricsPatch{},
&manager.Config{Image: imageName},
&kdefault.Kustomization{},
- &kdefault.ManagerAuthProxyPatch{},
&kdefault.ManagerConfigPatch{},
&prometheus.Kustomization{},
&prometheus.Monitor{},
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/enable_matrics_patch.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/enable_matrics_patch.go
new file mode 100644
index 00000000000..7a7a7e6a596
--- /dev/null
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/enable_matrics_patch.go
@@ -0,0 +1,61 @@
+/*
+Copyright 2020 The Kubernetes Authors.
+
+Licensed under the Apache License, Version 2.0 (the "License");
+you may not use this file except in compliance with the License.
+You may obtain a copy of the License at
+
+ http://www.apache.org/licenses/LICENSE-2.0
+
+Unless required by applicable law or agreed to in writing, software
+distributed under the License is distributed on an "AS IS" BASIS,
+WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+See the License for the specific language governing permissions and
+limitations under the License.
+*/
+
+package kdefault
+
+import (
+ "path/filepath"
+
+ "sigs.k8s.io/kubebuilder/v3/pkg/machinery"
+)
+
+var _ machinery.Template = &ManagerMetricsPatch{}
+
+// ManagerMetricsPatch scaffolds a file that defines the patch that enables prometheus metrics for the manager
+type ManagerMetricsPatch struct {
+ machinery.TemplateMixin
+ machinery.ComponentConfigMixin
+}
+
+// SetTemplateDefaults implements file.Template
+func (f *ManagerMetricsPatch) SetTemplateDefaults() error {
+ if f.Path == "" {
+ f.Path = filepath.Join("config", "default", "manager_metrics_patch.yaml")
+ }
+
+ f.TemplateBody = kustomizeMetricsPatchTemplate
+
+ f.IfExistsAction = machinery.Error
+
+ return nil
+}
+
+const kustomizeMetricsPatchTemplate = `# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
+`
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/kustomization.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/kustomization.go
index 319bcf1a6b3..5eccf772296 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/kustomization.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/kustomization.go
@@ -73,10 +73,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
{{ if .ComponentConfig -}}
# Mount the controller config file for loading manager configurations
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/manager_auth_proxy_patch.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/manager_auth_proxy_patch.go
deleted file mode 100644
index d8d57261952..00000000000
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/kdefault/manager_auth_proxy_patch.go
+++ /dev/null
@@ -1,87 +0,0 @@
-/*
-Copyright 2020 The Kubernetes Authors.
-
-Licensed under the Apache License, Version 2.0 (the "License");
-you may not use this file except in compliance with the License.
-You may obtain a copy of the License at
-
- http://www.apache.org/licenses/LICENSE-2.0
-
-Unless required by applicable law or agreed to in writing, software
-distributed under the License is distributed on an "AS IS" BASIS,
-WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
-See the License for the specific language governing permissions and
-limitations under the License.
-*/
-
-package kdefault
-
-import (
- "path/filepath"
-
- "sigs.k8s.io/kubebuilder/v3/pkg/machinery"
-)
-
-var _ machinery.Template = &ManagerAuthProxyPatch{}
-
-// ManagerAuthProxyPatch scaffolds a file that defines the patch that enables prometheus metrics for the manager
-type ManagerAuthProxyPatch struct {
- machinery.TemplateMixin
- machinery.ComponentConfigMixin
-}
-
-// SetTemplateDefaults implements file.Template
-func (f *ManagerAuthProxyPatch) SetTemplateDefaults() error {
- if f.Path == "" {
- f.Path = filepath.Join("config", "default", "manager_auth_proxy_patch.yaml")
- }
-
- f.TemplateBody = kustomizeAuthProxyPatchTemplate
-
- f.IfExistsAction = machinery.Error
-
- return nil
-}
-
-const kustomizeAuthProxyPatchTemplate = `# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
-{{- if not .ComponentConfig }}
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
-{{- end }}
-`
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/prometheus/monitor.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/prometheus/monitor.go
index 339ca03f072..68e599044f6 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/prometheus/monitor.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/prometheus/monitor.go
@@ -58,7 +58,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/kustomization.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/kustomization.go
index d3ea9b22fd9..4133078507f 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/kustomization.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/kustomization.go
@@ -54,10 +54,9 @@ const kustomizeRBACTemplate = `resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
`
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_client_role.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_client_role.go
similarity index 70%
rename from pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_client_role.go
rename to pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_client_role.go
index a348524ab4a..c178ab71ce7 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_client_role.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_client_role.go
@@ -22,26 +22,26 @@ import (
"sigs.k8s.io/kubebuilder/v3/pkg/machinery"
)
-var _ machinery.Template = &AuthProxyClientRole{}
+var _ machinery.Template = &MetricsClientRole{}
-// AuthProxyClientRole scaffolds a file that defines the role for the metrics reader
-type AuthProxyClientRole struct {
+// MetricsClientRole scaffolds a file that defines the role for the metrics reader
+type MetricsClientRole struct {
machinery.TemplateMixin
machinery.ProjectNameMixin
}
// SetTemplateDefaults implements file.Template
-func (f *AuthProxyClientRole) SetTemplateDefaults() error {
+func (f *MetricsClientRole) SetTemplateDefaults() error {
if f.Path == "" {
- f.Path = filepath.Join("config", "rbac", "auth_proxy_client_clusterrole.yaml")
+ f.Path = filepath.Join("config", "rbac", "metrics_client_cluster_role.yaml")
}
- f.TemplateBody = clientClusterRoleTemplate
+ f.TemplateBody = metricsClientClusterRoleTemplate
return nil
}
-const clientClusterRoleTemplate = `apiVersion: rbac.authorization.k8s.io/v1
+const metricsClientClusterRoleTemplate = `apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_role.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_role.go
similarity index 74%
rename from pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_role.go
rename to pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_role.go
index d1b639c0ee3..f45a39855d2 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_role.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_role.go
@@ -22,32 +22,32 @@ import (
"sigs.k8s.io/kubebuilder/v3/pkg/machinery"
)
-var _ machinery.Template = &AuthProxyRole{}
+var _ machinery.Template = &MetricsRole{}
-// AuthProxyRole scaffolds a file that defines the role for the auth proxy
-type AuthProxyRole struct {
+// MetricsRole scaffolds a file that defines the role for the auth proxy
+type MetricsRole struct {
machinery.TemplateMixin
machinery.ProjectNameMixin
}
// SetTemplateDefaults implements file.Template
-func (f *AuthProxyRole) SetTemplateDefaults() error {
+func (f *MetricsRole) SetTemplateDefaults() error {
if f.Path == "" {
- f.Path = filepath.Join("config", "rbac", "auth_proxy_role.yaml")
+ f.Path = filepath.Join("config", "rbac", "metrics_role.yaml")
}
- f.TemplateBody = proxyRoleTemplate
+ f.TemplateBody = metricsRoleTemplate
return nil
}
-const proxyRoleTemplate = `apiVersion: rbac.authorization.k8s.io/v1
+const metricsRoleTemplate = `apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
app.kubernetes.io/name: {{ .ProjectName }}
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_role_binding.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_role_binding.go
similarity index 69%
rename from pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_role_binding.go
rename to pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_role_binding.go
index 4ee86ed5c0f..9ea74c8679f 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_role_binding.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_role_binding.go
@@ -22,36 +22,36 @@ import (
"sigs.k8s.io/kubebuilder/v3/pkg/machinery"
)
-var _ machinery.Template = &AuthProxyRoleBinding{}
+var _ machinery.Template = &MonitoringBinding{}
-// AuthProxyRoleBinding scaffolds a file that defines the role binding for the auth proxy
-type AuthProxyRoleBinding struct {
+// MonitoringBinding scaffolds a file that defines the role binding for the auth proxy
+type MonitoringBinding struct {
machinery.TemplateMixin
machinery.ProjectNameMixin
}
// SetTemplateDefaults implements file.Template
-func (f *AuthProxyRoleBinding) SetTemplateDefaults() error {
+func (f *MonitoringBinding) SetTemplateDefaults() error {
if f.Path == "" {
- f.Path = filepath.Join("config", "rbac", "auth_proxy_role_binding.yaml")
+ f.Path = filepath.Join("config", "rbac", "metrics_role_binding.yaml")
}
- f.TemplateBody = proxyRoleBindinggTemplate
+ f.TemplateBody = metricsRoleBindinggTemplate
return nil
}
-const proxyRoleBindinggTemplate = `apiVersion: rbac.authorization.k8s.io/v1
+const metricsRoleBindinggTemplate = `apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
app.kubernetes.io/name: {{ .ProjectName }}
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_service.go b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_service.go
similarity index 75%
rename from pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_service.go
rename to pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_service.go
index 219efc86ed7..c5e5da558ed 100644
--- a/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/auth_proxy_service.go
+++ b/pkg/plugins/common/kustomize/v2/scaffolds/internal/templates/config/rbac/metrics_service.go
@@ -22,26 +22,26 @@ import (
"sigs.k8s.io/kubebuilder/v3/pkg/machinery"
)
-var _ machinery.Template = &AuthProxyService{}
+var _ machinery.Template = &MetricsService{}
-// AuthProxyService scaffolds a file that defines the service for the auth proxy
-type AuthProxyService struct {
+// MetricsService scaffolds a file that defines the service for the auth proxy
+type MetricsService struct {
machinery.TemplateMixin
machinery.ProjectNameMixin
}
// SetTemplateDefaults implements file.Template
-func (f *AuthProxyService) SetTemplateDefaults() error {
+func (f *MetricsService) SetTemplateDefaults() error {
if f.Path == "" {
- f.Path = filepath.Join("config", "rbac", "auth_proxy_service.yaml")
+ f.Path = filepath.Join("config", "rbac", "metrics_service.yaml")
}
- f.TemplateBody = authProxyServiceTemplate
+ f.TemplateBody = metricsServiceTemplate
return nil
}
-const authProxyServiceTemplate = `apiVersion: v1
+const metricsServiceTemplate = `apiVersion: v1
kind: Service
metadata:
labels:
diff --git a/test/e2e/v4/generate_test.go b/test/e2e/v4/generate_test.go
index 02f72b01910..9a8155ca84d 100644
--- a/test/e2e/v4/generate_test.go
+++ b/test/e2e/v4/generate_test.go
@@ -63,6 +63,10 @@ func GenerateV4(kbc *utils.TestContext) {
ExpectWithOffset(1, pluginutil.UncommentCode(
filepath.Join(kbc.Dir, "config", "default", "kustomization.yaml"),
"#- path: webhookcainjection_patch.yaml", "#")).To(Succeed())
+ ExpectWithOffset(1, pluginutil.UncommentCode(
+ filepath.Join(kbc.Dir, "config", "default", "kustomization.yaml"),
+ "#- path: manager_metrics_patch.yaml", "#")).To(Succeed())
+
ExpectWithOffset(1, pluginutil.UncommentCode(filepath.Join(kbc.Dir, "config", "default", "kustomization.yaml"),
certManagerTarget, "#")).To(Succeed())
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/default/kustomization.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/default/kustomization.yaml
index 2f78dfb54aa..b5f4c2a79b6 100644
--- a/testdata/project-v4-multigroup-with-deploy-image/config/default/kustomization.yaml
+++ b/testdata/project-v4-multigroup-with-deploy-image/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# [WEBHOOK] To enable webhook, uncomment all the sections with [WEBHOOK] prefix including the one in
# crd/kustomization.yaml
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/default/manager_auth_proxy_patch.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 4c3c27602f5..00000000000
--- a/testdata/project-v4-multigroup-with-deploy-image/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,39 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/default/manager_metrics_patch.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/testdata/project-v4-multigroup-with-deploy-image/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/prometheus/monitor.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/prometheus/monitor.yaml
index c7e880652bc..68b33ecd8b5 100644
--- a/testdata/project-v4-multigroup-with-deploy-image/config/prometheus/monitor.yaml
+++ b/testdata/project-v4-multigroup-with-deploy-image/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/kustomization.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/kustomization.yaml
index 08b359e46b5..5dc6fddec28 100644
--- a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/kustomization.yaml
+++ b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/kustomization.yaml
@@ -10,12 +10,11 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
# For each CRD, "Editor" and "Viewer" roles are scaffolded by
# default, aiding admins in cluster management. Those roles are
# not used by the Project itself. You can comment the following lines
@@ -40,3 +39,4 @@ resources:
- ship_frigate_viewer_role.yaml
- crew_captain_editor_role.yaml
- crew_captain_viewer_role.yaml
+
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_client_clusterrole.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_client_clusterrole.yaml
rename to testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_client_cluster_role.yaml
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_role.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_role.yaml
similarity index 94%
rename from testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_role.yaml
rename to testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_role.yaml
index 13038ff7689..82404922028 100644
--- a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_role.yaml
+++ b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-multigroup-with-deploy-image
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_role_binding.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_role_binding.yaml
similarity index 87%
rename from testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_role_binding.yaml
rename to testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_role_binding.yaml
index aae73208a49..e90cead25f4 100644
--- a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_role_binding.yaml
+++ b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-multigroup-with-deploy-image
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_service.yaml b/testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_service.yaml
similarity index 100%
rename from testdata/project-v4-multigroup-with-deploy-image/config/rbac/auth_proxy_service.yaml
rename to testdata/project-v4-multigroup-with-deploy-image/config/rbac/metrics_service.yaml
diff --git a/testdata/project-v4-multigroup-with-deploy-image/dist/install.yaml b/testdata/project-v4-multigroup-with-deploy-image/dist/install.yaml
index 26592d65d9a..46b43298a67 100644
--- a/testdata/project-v4-multigroup-with-deploy-image/dist/install.yaml
+++ b/testdata/project-v4-multigroup-with-deploy-image/dist/install.yaml
@@ -1208,7 +1208,7 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-multigroup-with-deploy-image
- name: project-v4-multigroup-with-deploy-image-proxy-role
+ name: project-v4-multigroup-with-deploy-image-metrics-role
rules:
- apiGroups:
- authentication.k8s.io
@@ -1512,11 +1512,11 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-multigroup-with-deploy-image
- name: project-v4-multigroup-with-deploy-image-proxy-rolebinding
+ name: project-v4-multigroup-with-deploy-image-metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: project-v4-multigroup-with-deploy-image-proxy-role
+ name: project-v4-multigroup-with-deploy-image-metrics-role
subjects:
- kind: ServiceAccount
name: project-v4-multigroup-with-deploy-image-controller-manager
@@ -1579,8 +1579,6 @@ spec:
spec:
containers:
- args:
- - --health-probe-bind-address=:8081
- - --metrics-bind-address=127.0.0.1:8080
- --leader-elect
command:
- /manager
@@ -1618,29 +1616,6 @@ spec:
- mountPath: /tmp/k8s-webhook-server/serving-certs
name: cert
readOnly: true
- - args:
- - --secure-listen-address=0.0.0.0:8443
- - --upstream=http://127.0.0.1:8080/
- - --logtostderr=true
- - --v=0
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- name: kube-rbac-proxy
- ports:
- - containerPort: 8443
- name: https
- protocol: TCP
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - ALL
securityContext:
runAsNonRoot: true
serviceAccountName: project-v4-multigroup-with-deploy-image-controller-manager
diff --git a/testdata/project-v4-multigroup/config/default/kustomization.yaml b/testdata/project-v4-multigroup/config/default/kustomization.yaml
index 9fe6e3630df..ac074b25f9c 100644
--- a/testdata/project-v4-multigroup/config/default/kustomization.yaml
+++ b/testdata/project-v4-multigroup/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# [WEBHOOK] To enable webhook, uncomment all the sections with [WEBHOOK] prefix including the one in
# crd/kustomization.yaml
diff --git a/testdata/project-v4-multigroup/config/default/manager_auth_proxy_patch.yaml b/testdata/project-v4-multigroup/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 4c3c27602f5..00000000000
--- a/testdata/project-v4-multigroup/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,39 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
diff --git a/testdata/project-v4-multigroup/config/default/manager_metrics_patch.yaml b/testdata/project-v4-multigroup/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/testdata/project-v4-multigroup/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/testdata/project-v4-multigroup/config/prometheus/monitor.yaml b/testdata/project-v4-multigroup/config/prometheus/monitor.yaml
index bb60c0d334a..443f65de517 100644
--- a/testdata/project-v4-multigroup/config/prometheus/monitor.yaml
+++ b/testdata/project-v4-multigroup/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/testdata/project-v4-multigroup/config/rbac/kustomization.yaml b/testdata/project-v4-multigroup/config/rbac/kustomization.yaml
index 08b359e46b5..5dc6fddec28 100644
--- a/testdata/project-v4-multigroup/config/rbac/kustomization.yaml
+++ b/testdata/project-v4-multigroup/config/rbac/kustomization.yaml
@@ -10,12 +10,11 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
# For each CRD, "Editor" and "Viewer" roles are scaffolded by
# default, aiding admins in cluster management. Those roles are
# not used by the Project itself. You can comment the following lines
@@ -40,3 +39,4 @@ resources:
- ship_frigate_viewer_role.yaml
- crew_captain_editor_role.yaml
- crew_captain_viewer_role.yaml
+
diff --git a/testdata/project-v4-multigroup/config/rbac/auth_proxy_client_clusterrole.yaml b/testdata/project-v4-multigroup/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from testdata/project-v4-multigroup/config/rbac/auth_proxy_client_clusterrole.yaml
rename to testdata/project-v4-multigroup/config/rbac/metrics_client_cluster_role.yaml
diff --git a/testdata/project-v4-multigroup/config/rbac/auth_proxy_role.yaml b/testdata/project-v4-multigroup/config/rbac/metrics_role.yaml
similarity index 94%
rename from testdata/project-v4-multigroup/config/rbac/auth_proxy_role.yaml
rename to testdata/project-v4-multigroup/config/rbac/metrics_role.yaml
index 56c97ddca82..a7b19928c33 100644
--- a/testdata/project-v4-multigroup/config/rbac/auth_proxy_role.yaml
+++ b/testdata/project-v4-multigroup/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-multigroup
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/testdata/project-v4-multigroup/config/rbac/auth_proxy_role_binding.yaml b/testdata/project-v4-multigroup/config/rbac/metrics_role_binding.yaml
similarity index 86%
rename from testdata/project-v4-multigroup/config/rbac/auth_proxy_role_binding.yaml
rename to testdata/project-v4-multigroup/config/rbac/metrics_role_binding.yaml
index 10f89301cdb..3af6d2f11cc 100644
--- a/testdata/project-v4-multigroup/config/rbac/auth_proxy_role_binding.yaml
+++ b/testdata/project-v4-multigroup/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-multigroup
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/testdata/project-v4-multigroup/config/rbac/auth_proxy_service.yaml b/testdata/project-v4-multigroup/config/rbac/metrics_service.yaml
similarity index 100%
rename from testdata/project-v4-multigroup/config/rbac/auth_proxy_service.yaml
rename to testdata/project-v4-multigroup/config/rbac/metrics_service.yaml
diff --git a/testdata/project-v4-multigroup/dist/install.yaml b/testdata/project-v4-multigroup/dist/install.yaml
index e2584bdeac2..e0331e1d27f 100644
--- a/testdata/project-v4-multigroup/dist/install.yaml
+++ b/testdata/project-v4-multigroup/dist/install.yaml
@@ -1208,7 +1208,7 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-multigroup
- name: project-v4-multigroup-proxy-role
+ name: project-v4-multigroup-metrics-role
rules:
- apiGroups:
- authentication.k8s.io
@@ -1512,11 +1512,11 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-multigroup
- name: project-v4-multigroup-proxy-rolebinding
+ name: project-v4-multigroup-metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: project-v4-multigroup-proxy-role
+ name: project-v4-multigroup-metrics-role
subjects:
- kind: ServiceAccount
name: project-v4-multigroup-controller-manager
@@ -1579,8 +1579,6 @@ spec:
spec:
containers:
- args:
- - --health-probe-bind-address=:8081
- - --metrics-bind-address=127.0.0.1:8080
- --leader-elect
command:
- /manager
@@ -1618,29 +1616,6 @@ spec:
- mountPath: /tmp/k8s-webhook-server/serving-certs
name: cert
readOnly: true
- - args:
- - --secure-listen-address=0.0.0.0:8443
- - --upstream=http://127.0.0.1:8080/
- - --logtostderr=true
- - --v=0
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- name: kube-rbac-proxy
- ports:
- - containerPort: 8443
- name: https
- protocol: TCP
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - ALL
securityContext:
runAsNonRoot: true
serviceAccountName: project-v4-multigroup-controller-manager
diff --git a/testdata/project-v4-with-deploy-image/config/default/kustomization.yaml b/testdata/project-v4-with-deploy-image/config/default/kustomization.yaml
index 62e78ccdbbe..a81c828747b 100644
--- a/testdata/project-v4-with-deploy-image/config/default/kustomization.yaml
+++ b/testdata/project-v4-with-deploy-image/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# [WEBHOOK] To enable webhook, uncomment all the sections with [WEBHOOK] prefix including the one in
# crd/kustomization.yaml
diff --git a/testdata/project-v4-with-deploy-image/config/default/manager_auth_proxy_patch.yaml b/testdata/project-v4-with-deploy-image/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 4c3c27602f5..00000000000
--- a/testdata/project-v4-with-deploy-image/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,39 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
diff --git a/testdata/project-v4-with-deploy-image/config/default/manager_metrics_patch.yaml b/testdata/project-v4-with-deploy-image/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/testdata/project-v4-with-deploy-image/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/testdata/project-v4-with-deploy-image/config/prometheus/monitor.yaml b/testdata/project-v4-with-deploy-image/config/prometheus/monitor.yaml
index 0f805f2c2e7..51baef4b2e0 100644
--- a/testdata/project-v4-with-deploy-image/config/prometheus/monitor.yaml
+++ b/testdata/project-v4-with-deploy-image/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/testdata/project-v4-with-deploy-image/config/rbac/kustomization.yaml b/testdata/project-v4-with-deploy-image/config/rbac/kustomization.yaml
index 67076dab990..3f08cb60620 100644
--- a/testdata/project-v4-with-deploy-image/config/rbac/kustomization.yaml
+++ b/testdata/project-v4-with-deploy-image/config/rbac/kustomization.yaml
@@ -10,12 +10,11 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
# For each CRD, "Editor" and "Viewer" roles are scaffolded by
# default, aiding admins in cluster management. Those roles are
# not used by the Project itself. You can comment the following lines
@@ -24,3 +23,4 @@ resources:
- busybox_viewer_role.yaml
- memcached_editor_role.yaml
- memcached_viewer_role.yaml
+
diff --git a/testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_client_clusterrole.yaml b/testdata/project-v4-with-deploy-image/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_client_clusterrole.yaml
rename to testdata/project-v4-with-deploy-image/config/rbac/metrics_client_cluster_role.yaml
diff --git a/testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_role.yaml b/testdata/project-v4-with-deploy-image/config/rbac/metrics_role.yaml
similarity index 94%
rename from testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_role.yaml
rename to testdata/project-v4-with-deploy-image/config/rbac/metrics_role.yaml
index 438d9bd0702..690aba51194 100644
--- a/testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_role.yaml
+++ b/testdata/project-v4-with-deploy-image/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-with-deploy-image
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_role_binding.yaml b/testdata/project-v4-with-deploy-image/config/rbac/metrics_role_binding.yaml
similarity index 87%
rename from testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_role_binding.yaml
rename to testdata/project-v4-with-deploy-image/config/rbac/metrics_role_binding.yaml
index 3be0002395d..caba0e4981c 100644
--- a/testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_role_binding.yaml
+++ b/testdata/project-v4-with-deploy-image/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-with-deploy-image
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_service.yaml b/testdata/project-v4-with-deploy-image/config/rbac/metrics_service.yaml
similarity index 100%
rename from testdata/project-v4-with-deploy-image/config/rbac/auth_proxy_service.yaml
rename to testdata/project-v4-with-deploy-image/config/rbac/metrics_service.yaml
diff --git a/testdata/project-v4-with-deploy-image/dist/install.yaml b/testdata/project-v4-with-deploy-image/dist/install.yaml
index 70babe98cbe..8a820153db9 100644
--- a/testdata/project-v4-with-deploy-image/dist/install.yaml
+++ b/testdata/project-v4-with-deploy-image/dist/install.yaml
@@ -534,7 +534,7 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-with-deploy-image
- name: project-v4-with-deploy-image-proxy-role
+ name: project-v4-with-deploy-image-metrics-role
rules:
- apiGroups:
- authentication.k8s.io
@@ -588,11 +588,11 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-with-deploy-image
- name: project-v4-with-deploy-image-proxy-rolebinding
+ name: project-v4-with-deploy-image-metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: project-v4-with-deploy-image-proxy-role
+ name: project-v4-with-deploy-image-metrics-role
subjects:
- kind: ServiceAccount
name: project-v4-with-deploy-image-controller-manager
@@ -655,8 +655,6 @@ spec:
spec:
containers:
- args:
- - --health-probe-bind-address=:8081
- - --metrics-bind-address=127.0.0.1:8080
- --leader-elect
command:
- /manager
@@ -699,29 +697,6 @@ spec:
- mountPath: /tmp/k8s-webhook-server/serving-certs
name: cert
readOnly: true
- - args:
- - --secure-listen-address=0.0.0.0:8443
- - --upstream=http://127.0.0.1:8080/
- - --logtostderr=true
- - --v=0
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- name: kube-rbac-proxy
- ports:
- - containerPort: 8443
- name: https
- protocol: TCP
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - ALL
securityContext:
runAsNonRoot: true
serviceAccountName: project-v4-with-deploy-image-controller-manager
diff --git a/testdata/project-v4-with-grafana/config/default/kustomization.yaml b/testdata/project-v4-with-grafana/config/default/kustomization.yaml
index 7fca0820b0c..b6daeb7047d 100644
--- a/testdata/project-v4-with-grafana/config/default/kustomization.yaml
+++ b/testdata/project-v4-with-grafana/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# [WEBHOOK] To enable webhook, uncomment all the sections with [WEBHOOK] prefix including the one in
# crd/kustomization.yaml
diff --git a/testdata/project-v4-with-grafana/config/default/manager_auth_proxy_patch.yaml b/testdata/project-v4-with-grafana/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 4c3c27602f5..00000000000
--- a/testdata/project-v4-with-grafana/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,39 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
diff --git a/testdata/project-v4-with-grafana/config/default/manager_metrics_patch.yaml b/testdata/project-v4-with-grafana/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/testdata/project-v4-with-grafana/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/testdata/project-v4-with-grafana/config/prometheus/monitor.yaml b/testdata/project-v4-with-grafana/config/prometheus/monitor.yaml
index 8505bfa5bfc..47e4734ad4d 100644
--- a/testdata/project-v4-with-grafana/config/prometheus/monitor.yaml
+++ b/testdata/project-v4-with-grafana/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/testdata/project-v4-with-grafana/config/rbac/kustomization.yaml b/testdata/project-v4-with-grafana/config/rbac/kustomization.yaml
index 731832a6ac3..9109783ed39 100644
--- a/testdata/project-v4-with-grafana/config/rbac/kustomization.yaml
+++ b/testdata/project-v4-with-grafana/config/rbac/kustomization.yaml
@@ -10,9 +10,8 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
diff --git a/testdata/project-v4-with-grafana/config/rbac/auth_proxy_client_clusterrole.yaml b/testdata/project-v4-with-grafana/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from testdata/project-v4-with-grafana/config/rbac/auth_proxy_client_clusterrole.yaml
rename to testdata/project-v4-with-grafana/config/rbac/metrics_client_cluster_role.yaml
diff --git a/testdata/project-v4-with-grafana/config/rbac/auth_proxy_role.yaml b/testdata/project-v4-with-grafana/config/rbac/metrics_role.yaml
similarity index 94%
rename from testdata/project-v4-with-grafana/config/rbac/auth_proxy_role.yaml
rename to testdata/project-v4-with-grafana/config/rbac/metrics_role.yaml
index 979bc272f7a..44a25d5fb06 100644
--- a/testdata/project-v4-with-grafana/config/rbac/auth_proxy_role.yaml
+++ b/testdata/project-v4-with-grafana/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-with-grafana
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/testdata/project-v4-with-grafana/config/rbac/auth_proxy_role_binding.yaml b/testdata/project-v4-with-grafana/config/rbac/metrics_role_binding.yaml
similarity index 87%
rename from testdata/project-v4-with-grafana/config/rbac/auth_proxy_role_binding.yaml
rename to testdata/project-v4-with-grafana/config/rbac/metrics_role_binding.yaml
index b5302ea3805..cd500e72cf2 100644
--- a/testdata/project-v4-with-grafana/config/rbac/auth_proxy_role_binding.yaml
+++ b/testdata/project-v4-with-grafana/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project-v4-with-grafana
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/testdata/project-v4-with-grafana/config/rbac/auth_proxy_service.yaml b/testdata/project-v4-with-grafana/config/rbac/metrics_service.yaml
similarity index 100%
rename from testdata/project-v4-with-grafana/config/rbac/auth_proxy_service.yaml
rename to testdata/project-v4-with-grafana/config/rbac/metrics_service.yaml
diff --git a/testdata/project-v4-with-grafana/dist/install.yaml b/testdata/project-v4-with-grafana/dist/install.yaml
index 5877a647805..f832955adc9 100644
--- a/testdata/project-v4-with-grafana/dist/install.yaml
+++ b/testdata/project-v4-with-grafana/dist/install.yaml
@@ -93,7 +93,7 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-with-grafana
- name: project-v4-with-grafana-proxy-role
+ name: project-v4-with-grafana-metrics-role
rules:
- apiGroups:
- authentication.k8s.io
@@ -147,11 +147,11 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4-with-grafana
- name: project-v4-with-grafana-proxy-rolebinding
+ name: project-v4-with-grafana-metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: project-v4-with-grafana-proxy-role
+ name: project-v4-with-grafana-metrics-role
subjects:
- kind: ServiceAccount
name: project-v4-with-grafana-controller-manager
@@ -198,31 +198,6 @@ spec:
spec:
containers:
- args:
- - --secure-listen-address=0.0.0.0:8443
- - --upstream=http://127.0.0.1:8080/
- - --logtostderr=true
- - --v=0
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- name: kube-rbac-proxy
- ports:
- - containerPort: 8443
- name: https
- protocol: TCP
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - ALL
- - args:
- - --health-probe-bind-address=:8081
- - --metrics-bind-address=127.0.0.1:8080
- --leader-elect
command:
- /manager
diff --git a/testdata/project-v4/config/default/kustomization.yaml b/testdata/project-v4/config/default/kustomization.yaml
index ae7fc170730..45e22d821f0 100644
--- a/testdata/project-v4/config/default/kustomization.yaml
+++ b/testdata/project-v4/config/default/kustomization.yaml
@@ -27,10 +27,9 @@ resources:
#- ../prometheus
patches:
-# Protect the /metrics endpoint by putting it behind auth.
-# If you want your controller-manager to expose the /metrics
-# endpoint w/o any authn/z, please comment the following line.
-- path: manager_auth_proxy_patch.yaml
+# [METRICS] The following patch will enable the metrics endpoint. Ensure that you also protect this endpoint.
+# If you want to expose the metric endpoint of your controller-manager uncomment the following line.
+#- path: manager_metrics_patch.yaml
# [WEBHOOK] To enable webhook, uncomment all the sections with [WEBHOOK] prefix including the one in
# crd/kustomization.yaml
diff --git a/testdata/project-v4/config/default/manager_auth_proxy_patch.yaml b/testdata/project-v4/config/default/manager_auth_proxy_patch.yaml
deleted file mode 100644
index 4c3c27602f5..00000000000
--- a/testdata/project-v4/config/default/manager_auth_proxy_patch.yaml
+++ /dev/null
@@ -1,39 +0,0 @@
-# This patch inject a sidecar container which is a HTTP proxy for the
-# controller manager, it performs RBAC authorization against the Kubernetes API using SubjectAccessReviews.
-apiVersion: apps/v1
-kind: Deployment
-metadata:
- name: controller-manager
- namespace: system
-spec:
- template:
- spec:
- containers:
- - name: kube-rbac-proxy
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - "ALL"
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- args:
- - "--secure-listen-address=0.0.0.0:8443"
- - "--upstream=http://127.0.0.1:8080/"
- - "--logtostderr=true"
- - "--v=0"
- ports:
- - containerPort: 8443
- protocol: TCP
- name: https
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- - name: manager
- args:
- - "--health-probe-bind-address=:8081"
- - "--metrics-bind-address=127.0.0.1:8080"
- - "--leader-elect"
diff --git a/testdata/project-v4/config/default/manager_metrics_patch.yaml b/testdata/project-v4/config/default/manager_metrics_patch.yaml
new file mode 100644
index 00000000000..c23d8d9268f
--- /dev/null
+++ b/testdata/project-v4/config/default/manager_metrics_patch.yaml
@@ -0,0 +1,15 @@
+# This patch adds the args to allow expose the metrics endpoint
+apiVersion: apps/v1
+kind: Deployment
+metadata:
+ name: controller-manager
+ namespace: system
+spec:
+ template:
+ spec:
+ containers:
+ - name: manager
+ args:
+ - "--health-probe-bind-address=:8081"
+ - "--metrics-bind-address=0.0.0.0:8080"
+ - "--leader-elect"
diff --git a/testdata/project-v4/config/prometheus/monitor.yaml b/testdata/project-v4/config/prometheus/monitor.yaml
index 767555588d4..508a47f266c 100644
--- a/testdata/project-v4/config/prometheus/monitor.yaml
+++ b/testdata/project-v4/config/prometheus/monitor.yaml
@@ -15,7 +15,7 @@ spec:
scheme: https
bearerTokenFile: /var/run/secrets/kubernetes.io/serviceaccount/token
tlsConfig:
- insecureSkipVerify: true
+ insecureSkipVerify: true # TODO(user): Not use this configuration for production
selector:
matchLabels:
control-plane: controller-manager
diff --git a/testdata/project-v4/config/rbac/kustomization.yaml b/testdata/project-v4/config/rbac/kustomization.yaml
index 8518bf9e24d..59b33241e4c 100644
--- a/testdata/project-v4/config/rbac/kustomization.yaml
+++ b/testdata/project-v4/config/rbac/kustomization.yaml
@@ -10,12 +10,11 @@ resources:
- leader_election_role.yaml
- leader_election_role_binding.yaml
# Comment the following 4 lines if you want to disable
-# the auth proxy (https://github.com/brancz/kube-rbac-proxy)
-# which protects your /metrics endpoint.
-- auth_proxy_service.yaml
-- auth_proxy_role.yaml
-- auth_proxy_role_binding.yaml
-- auth_proxy_client_clusterrole.yaml
+# the metrics which protects your /metrics endpoint.
+- metrics_service.yaml
+- metrics_role.yaml
+- metrics_role_binding.yaml
+- metrics_client_cluster_role.yaml
# For each CRD, "Editor" and "Viewer" roles are scaffolded by
# default, aiding admins in cluster management. Those roles are
# not used by the Project itself. You can comment the following lines
@@ -26,3 +25,4 @@ resources:
- firstmate_viewer_role.yaml
- captain_editor_role.yaml
- captain_viewer_role.yaml
+
diff --git a/testdata/project-v4/config/rbac/auth_proxy_client_clusterrole.yaml b/testdata/project-v4/config/rbac/metrics_client_cluster_role.yaml
similarity index 100%
rename from testdata/project-v4/config/rbac/auth_proxy_client_clusterrole.yaml
rename to testdata/project-v4/config/rbac/metrics_client_cluster_role.yaml
diff --git a/testdata/project-v4/config/rbac/auth_proxy_role.yaml b/testdata/project-v4/config/rbac/metrics_role.yaml
similarity index 94%
rename from testdata/project-v4/config/rbac/auth_proxy_role.yaml
rename to testdata/project-v4/config/rbac/metrics_role.yaml
index 43aa96480ad..22183eb2b2e 100644
--- a/testdata/project-v4/config/rbac/auth_proxy_role.yaml
+++ b/testdata/project-v4/config/rbac/metrics_role.yaml
@@ -4,7 +4,7 @@ metadata:
labels:
app.kubernetes.io/name: project-v4
app.kubernetes.io/managed-by: kustomize
- name: proxy-role
+ name: metrics-role
rules:
- apiGroups:
- authentication.k8s.io
diff --git a/testdata/project-v4/config/rbac/auth_proxy_role_binding.yaml b/testdata/project-v4/config/rbac/metrics_role_binding.yaml
similarity index 86%
rename from testdata/project-v4/config/rbac/auth_proxy_role_binding.yaml
rename to testdata/project-v4/config/rbac/metrics_role_binding.yaml
index e5bbe0214cd..a5d55acfa29 100644
--- a/testdata/project-v4/config/rbac/auth_proxy_role_binding.yaml
+++ b/testdata/project-v4/config/rbac/metrics_role_binding.yaml
@@ -4,11 +4,11 @@ metadata:
labels:
app.kubernetes.io/name: project-v4
app.kubernetes.io/managed-by: kustomize
- name: proxy-rolebinding
+ name: metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: proxy-role
+ name: metrics-role
subjects:
- kind: ServiceAccount
name: controller-manager
diff --git a/testdata/project-v4/config/rbac/auth_proxy_service.yaml b/testdata/project-v4/config/rbac/metrics_service.yaml
similarity index 100%
rename from testdata/project-v4/config/rbac/auth_proxy_service.yaml
rename to testdata/project-v4/config/rbac/metrics_service.yaml
diff --git a/testdata/project-v4/dist/install.yaml b/testdata/project-v4/dist/install.yaml
index 4466171f902..5601a85da95 100644
--- a/testdata/project-v4/dist/install.yaml
+++ b/testdata/project-v4/dist/install.yaml
@@ -528,7 +528,7 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4
- name: project-v4-proxy-role
+ name: project-v4-metrics-role
rules:
- apiGroups:
- authentication.k8s.io
@@ -582,11 +582,11 @@ metadata:
labels:
app.kubernetes.io/managed-by: kustomize
app.kubernetes.io/name: project-v4
- name: project-v4-proxy-rolebinding
+ name: project-v4-metrics-rolebinding
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
- name: project-v4-proxy-role
+ name: project-v4-metrics-role
subjects:
- kind: ServiceAccount
name: project-v4-controller-manager
@@ -649,8 +649,6 @@ spec:
spec:
containers:
- args:
- - --health-probe-bind-address=:8081
- - --metrics-bind-address=127.0.0.1:8080
- --leader-elect
command:
- /manager
@@ -688,29 +686,6 @@ spec:
- mountPath: /tmp/k8s-webhook-server/serving-certs
name: cert
readOnly: true
- - args:
- - --secure-listen-address=0.0.0.0:8443
- - --upstream=http://127.0.0.1:8080/
- - --logtostderr=true
- - --v=0
- image: gcr.io/kubebuilder/kube-rbac-proxy:v0.16.0
- name: kube-rbac-proxy
- ports:
- - containerPort: 8443
- name: https
- protocol: TCP
- resources:
- limits:
- cpu: 500m
- memory: 128Mi
- requests:
- cpu: 5m
- memory: 64Mi
- securityContext:
- allowPrivilegeEscalation: false
- capabilities:
- drop:
- - ALL
securityContext:
runAsNonRoot: true
serviceAccountName: project-v4-controller-manager
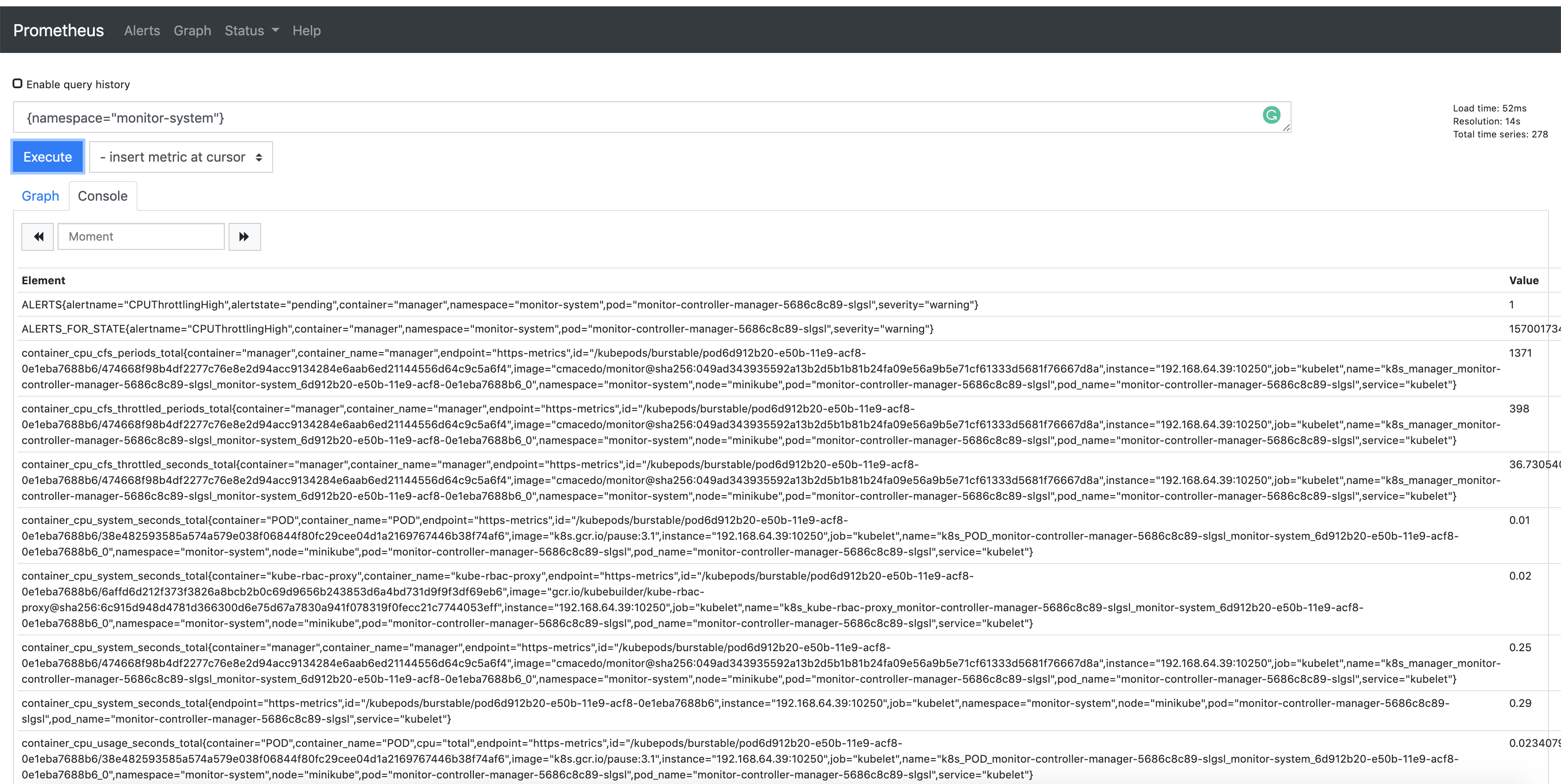 +## Consuming the Metrics from other Pods.
+
+Then, see an example to create a Pod using Curl to reach out the metrics:
+
+```sh
+kubectl run curl --restart=Never -n
+## Consuming the Metrics from other Pods.
+
+Then, see an example to create a Pod using Curl to reach out the metrics:
+
+```sh
+kubectl run curl --restart=Never -n