This repository contains a collaboration of general and specific Amazon Web Services CloudFormation Template Examples. The basic design is a layered approach so there is less repeat content between all the templates. That way you can build a custom environment by picking the solution templates you wish to use. In other words you won't see a VPC created over and over throughout the templates. You simply use the VPC template then move to the next piece you would like to create.
Also, The general design leans towards not having to refactor the template to fit your account/environment. By using the configured parameters from the console or CLI you should be able to use the template without the need to edit it. The templates generally output all the information you may need for another template. So, be sure to examine the Outputs tab after creating the stack.
The AWS CLI examples can be dropped in a shell script and/or added to your CI/CD solution to spin up solutions in a fully automated fashion. Of course logic around updating stacks, deleting and checking for success/failure should be addressed.
With a simple shell script and a customized parameter json file you can spin up stacks quickly and consistently. Furthermore it's just as easy to tear a CloudFormation stack versus if all the objects where created manually.
One template to rule them all... These are master templates that call nested templates. These are good to build out a full environment without having to run each template individually. Coupled with a custom parameters JSON file can give you a one command solution to a complex setup and eliminate the need to duplicate code.
For instance you could have a VPC, NAT, RDS and Autoscaling Webapp behind an ELB and Update DNS all in one command using various foundational templates that I've creates to be used together.
|
Select the foundational pieces for building out an infrastructure from the ground up.
|
|
||||||
|
|||||||
|
Creates an entire VPC from scratch for Lab or Permanent.
|
|
||||||
|
|||||||
|
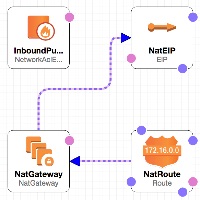
Creates a NAT Gateway on an existing VPC with Public (IGW) and Private subnets. Private route table is updated to route traffic to the NAT gateway a Public subnet that has an Internet Gateway Attached.
|
|
||||||
|
|||||||
|
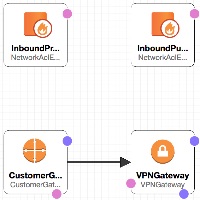
Creates a Site-to-Site BGP VPN Connection in and existing VPC with public and/or private networks. There is an option to not exclude allowing VPN access to the public networks. Simply select false for the 'Include Public Subnets', leave default value in Public Network ACL and Route Table. The values will just be ignored. This only sets up the AWS side of the VPN. After the CloudFormation creates the objects you'll then need to configure your remote VPN Device. Here's an article that gives the configuration steps for configuring a Sophos UTM v9 VPN endpoint. This assumes that the Private Network ACL allows all outbound. Lastly, the Private Network ACL inbound is updated to allow the remote network block specified.
|
|
||||||
|
|||||||
|
Creates a single Bastion host on a Public subnet in an existing VPC. Select from either a RHEL, Ubuntu or Windows OS.
|
|
||||||
|
|||||||
|
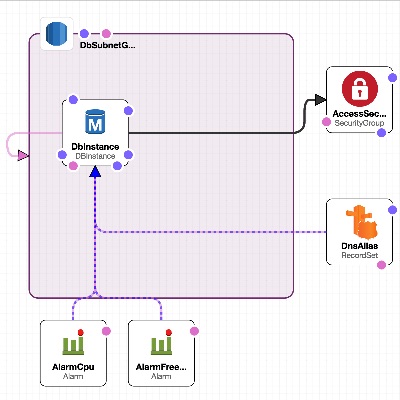
Creates a MySQL RDS Database Instance.
|
|
||||||
|
|||||||
|
Create an Autoscaling group in 3 private subnets from a baked AMI, an Elastic Load Balancer in 3 public subnets and S3 ELB Logging Bucket. Option to use SSL/TLS on ELB. Option to update Route 53 Hosted DNS alias to point to the ELB. Setup to add RDS Access Security Group. Does not create an RDS Instance. Use an RDS Instance Cloudformation Template first.
|
|
||||||
|
|||||||
|
Create an Autoscaling group in 3 private subnets from a baked AMI, an Elastic Load Balancer in 3 public subnets and S3 ELB Logging Bucket. Option to use SSL/TLS on ELB. Option to update Route 53 Hosted DNS alias to point to the ELB.
|
|
||||||
|
|||||||
<tr>
<th align="left" colspan="2"><h4><a href="https://github.com/stelligent/cloudformation_templates/tree/master/labs/ecs">EC2 Container Service Lab</a></h4></th>
</tr>
<tr>
<td valign="top">
<p>Automates the integration between EC2 Container Service (ECS), EC2 Container Registry (ECR), CodeCommit, and CodePipeline</p>
<h6>Prerequisites</h6>
<ol>
<li>EC2 Key Pair</li>
<li>Existing Docker Image</li>
<li>CodeCommit Repository</li>
<li>ECR Repository</li>
</ol>
<h6>Supported Regions</h6>
<ol>
<li>us-east-1</li>
</ol>
<h6>Create Details</h6>
<ol>
<li>Virtual Private Cloud (VPC) (and associated resources)</li>
<li>Auto Scaling Group, Auto Scaling Launch Configuration</li>
<li>ECS Cluster, ECS Service, ECS Task Definition</li>
<li>Elastic Load Balancer</li>
<li>IAM Instance Profile, IAM Roles</li>
<li>EC2 Instance (Jenkins, Docker)</li>
<li>CodePipeline with CodeCommit Integration</li>
</ol>
</td>
<td nowrap width="200" valign="top">
<table>
<tr>
<th align="left">Launch</th>
</tr>
<tr>
<td>
<a href="https://console.aws.amazon.com/cloudformation/home?region=us-east-1#/stacks/new?&templateURL=https://s3.amazonaws.com/stelligent-public/cloudformation-templates/github/labs/ecs/ecs-pipeline.json" target="_blank"><img src="https://s3.amazonaws.com/stelligent-public/media/images/buttons/cloudformation-launch-stack-button.png"></a>
<p>us-east-1</p>
</td>
</tr>
</table>
<table>
<tr>
<th align="left">View in Designer</th>
</tr>
<tr>
<td>
<a href="https://console.aws.amazon.com/cloudformation/designer/home?region=us-east-1&templateURL=https://s3.amazonaws.com/stelligent-public/cloudformation-templates/github/labs/ecs/ecs-pipeline.json" target="_blank"><img src="https://s3.amazonaws.com/stelligent-public/media/cloudformation-diagrams/ecs_codepipeline.jpg" width:100% alt="View in Designer"></a>
</td>
</tr>
</table>
<table>
<tr>
<th align="left">How To Video</th>
</tr>
<tr>
<td>
<img src="https://s3.amazonaws.com/stelligent-public/media/images/screenshots/HowTo_Stelligent_YouTube_144x81.jpg" width:100% alt="HowTo Video"></a>
<p>COMING SOON</p>
</td>
</tr>
</table>
</td>
</tr>
<tr>
<td colspan="2">
<table>
<tr>
<th align="left">AWS CLI Example</th>
</tr>
<tr>
<td>
<h6>Base Command</h6>
<code>aws cloudformation create-stack --profile {AWS Profile Name} --stack-name {Stack Name} --capabilities CAPABILITY_IAM --template-url "https://s3.amazonaws.com/stelligent-public/cloudformation-templates/github/labs/ecs/ecs-pipeline.json"</code>
</td>
</tr>
<tr>
<td>
<h5>Parameters</h5>
</td>
</tr>
<tr>
<td>
<h6>Option 1 - Custom Parameters JSON File <a href="https://github.com/stelligent/cloudformation_templates/blob/master/labs/ecs/example-parameters.json">(Example Here)</a></h6>
<code>--parameters file:///localpath/to/custom-parameters.json</code>
</td>
</tr>
<tr>
<td>
<h6>Option 2 - Pass Parameters on CLI</h6>
</td>
</tr>
<tr>
<td>
<code> --parameters ParameterKey=RepositoryName,ParameterValue=YOURCCREPO ParameterKey=RepositoryBranch,ParameterValue=master ParameterKey=KeyName,ParameterValue=YOUREC2KEYPAIR ParameterKey=YourIP,ParameterValue=YOURIP/32 ParameterKey=ECSRepoName,ParameterValue=YOURECRREPO ParameterKey=ECSCFNURL,ParameterValue=NOURL ParameterKey=AppName,ParameterValue=app-name-1648"</code>
</td>
</tr>
</table>
</td>
</tr>
<tr>
<th align="left" colspan="2"><h4><a href="https://github.com/stelligent/cloudformation_templates/blob/master/labs/test_instances/rhel-ubuntu-win2012.template">Test Instances</a></h4></th>
</tr>
<tr>
<td valign="top">
<p>Creates three test instances in an existing VPC. Each instance is a different operating system. They are; Red Hat Enterprise Linux 7, Ubuntu 14 and Windows 2012 R2.</p>
<h6>Create Details</h6>
<ol>
<li>3 EC2 Instances</li>
<li>IAM Role</li>
<li>IAM Instance Profile</li>
</ol>
</td>
<td nowrap width="200" valign="top">
<table>
<tr>
<th align="left">Launch</th>
</tr>
<tr>
<td>
<a href="https://console.aws.amazon.com/cloudformation/home?region=us-west-2#/stacks/new?&templateURL=https://s3.amazonaws.com/stelligent-public/cloudformation-templates/github/labs/test_instances/rhel-ubuntu-win2012.template" target="_blank"><img src="https://s3.amazonaws.com/stelligent-public/media/images/buttons/cloudformation-launch-stack-button.png"></a>
<p>us-west-2</p>
<a href="https://console.aws.amazon.com/cloudformation/home?region=us-east-1#/stacks/new?&templateURL=https://s3.amazonaws.com/stelligent-public/cloudformation-templates/github/labs/test_instances/rhel-ubuntu-win2012.template" target="_blank"><img src="https://s3.amazonaws.com/stelligent-public/media/images/buttons/cloudformation-launch-stack-button.png"></a>
<p>us-east-1</p>
</td>
</tr>
</table>
<table>
<tr>
<th align="left">View in Designer</th>
</tr>
<tr>
<td>
<a href="https://console.aws.amazon.com/cloudformation/designer/home?region=us-west-2&templateURL=https://s3.amazonaws.com/stelligent-public/cloudformation-templates/github/labs/test_instances/rhel-ubuntu-win2012.template" target="_blank"><img src="https://s3.amazonaws.com/stelligent-public/media/cloudformation-diagrams/test-instances-200x200.jpg" width:100% alt="View in Designer"></a>
</td>
</tr>
</table>
<table>
<tr>
<th align="left">How To Video</th>
</tr>
<tr>
<td>
<img src="https://s3.amazonaws.com/stelligent-public/media/images/screenshots/HowTo_Stelligent_YouTube_144x81.jpg" width:100% alt="HowTo Video"></a>
<p>COMING SOON</p>
</td>
</tr>
</table>
</td>
</tr>
<tr>
<td colspan="2">
<table>
<tr>
<th align="left">AWS CLI Example</th>
</tr>
<tr>
<td>
<h6>Base Command</h6>
<code>aws cloudformation create-stack --profile {AWS Profile Name} --stack-name {Stack Name} --capabilities CAPABILITY_IAM --template-url "https://s3.amazonaws.com/stelligent-public/cloudformation-templates/github/labs/test_instances/rhel-ubuntu-win2012.template"</code>
</td>
</tr>
<tr>
<td>
<h5>Parameters</h5>
</td>
</tr>
<tr>
<td>
<h6>Option 1 - Custom Parameters JSON File <a href="https://github.com/stelligent/cloudformation_templates/blob/master/labs/test_instances/example-parameters.json">(Example Here)</a></h6>
<code>--parameters file:///localpath/to/custom-parameters.json</code>
</td>
</tr>
<tr>
<td>
<h6>Option 2 - Pass Parameters on CLI</h6>
</td>
</tr>
<tr>
<td>
<code>--parameters ... COMING SOON</code>
</td>
</tr>
</table>
</td>
</tr>
|
Creates a Chef Complianc Web server in a Public Subnet with Internet Gatewayy attached on an existing VPC. It then attaches an EIP and finally adds the instance to an existing instance-to-instance security group.
|
|
||||||||
|
|||||||||
|
Creates a Bitbucket Server in a private or public subnet in an existing VPC.
|
|
||||||||
|
|||||||||
|
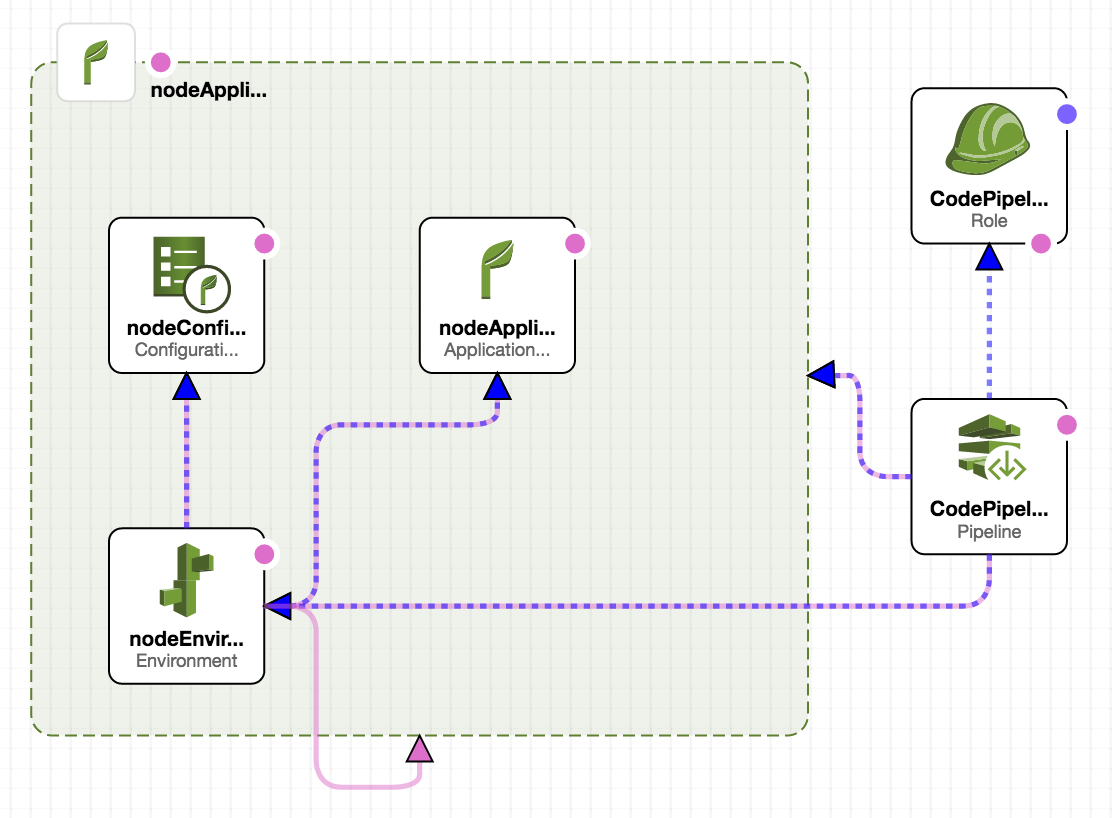
Automates the integration between AWS Elastic Beanstalk and CodePipeline
|
|
||||||||
|
|||||||||
|
Automates the integration between AWS CodeCommit and CodePipeline
|
|
||||||||
|
|||||||||
|
Automates the integration between AWS Lambda and CodePipeline
|
|
||||||||
|
|||||||||
|
Automates the integration between AWS OpsWorks, CodeCommit and CodePipeline
|
|
||||||||
|
|||||||||
|
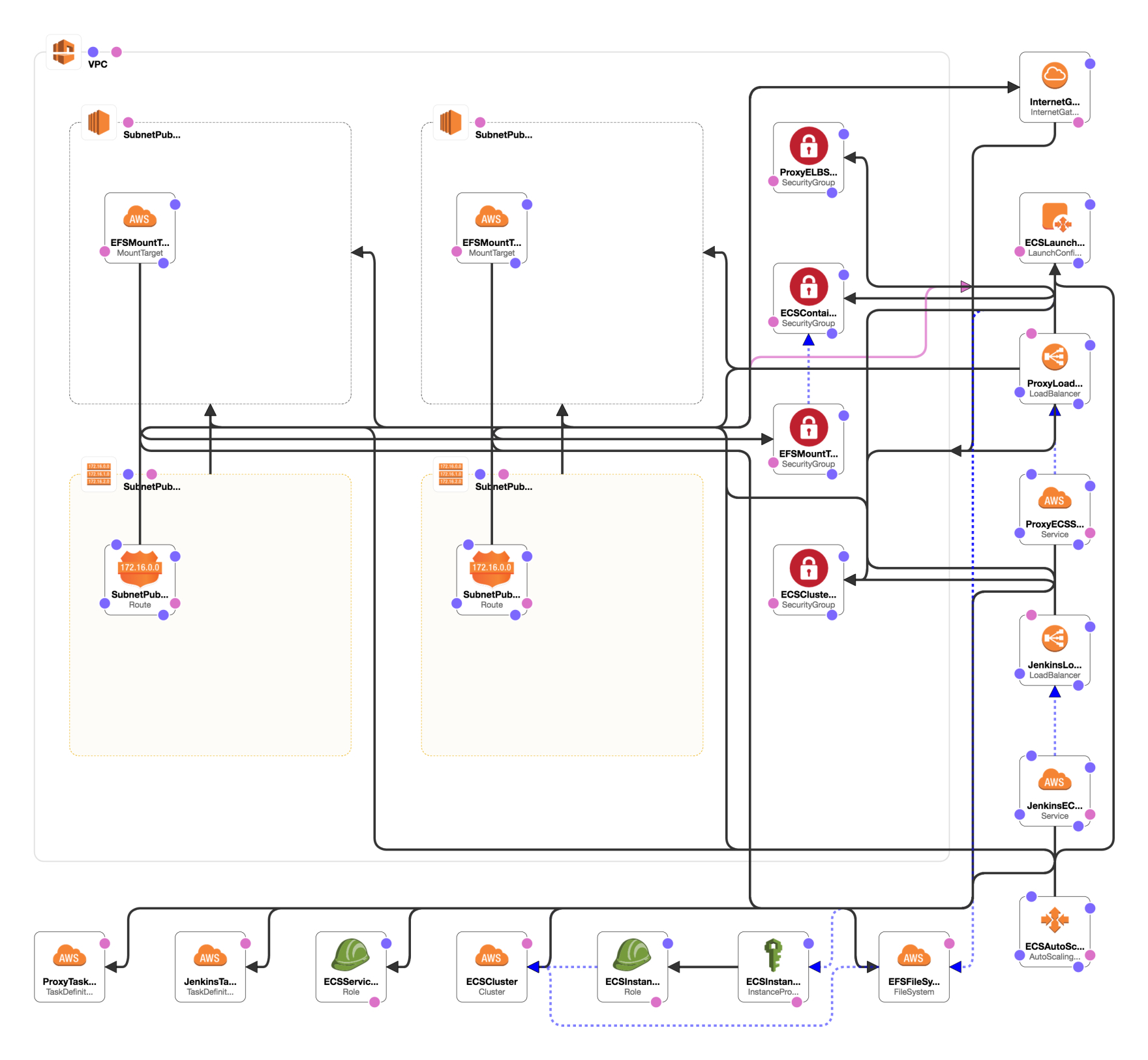
Containerized CI Solutions in AWS: Jenkins in ECS
|
|
||||||||
|
|||||||||