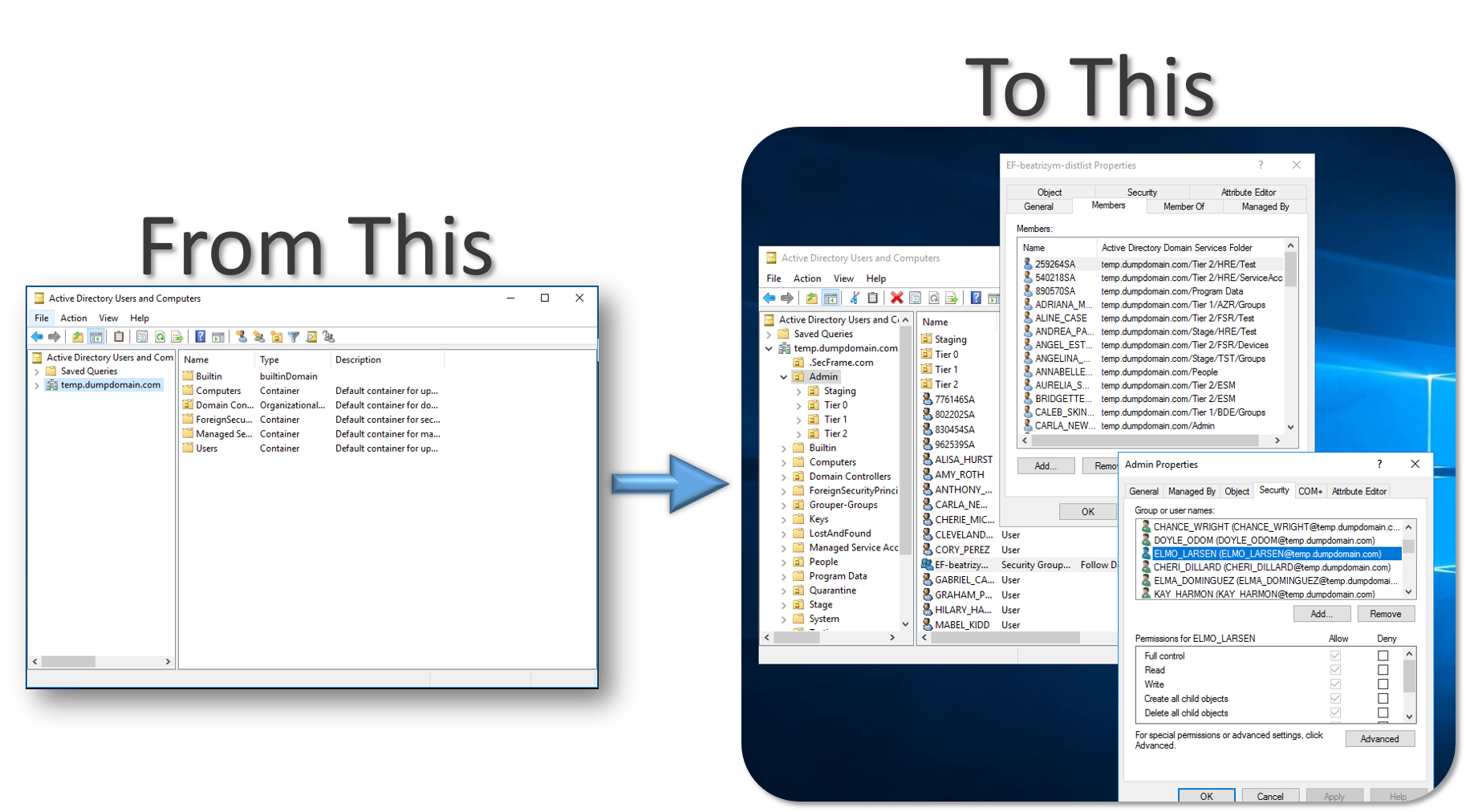
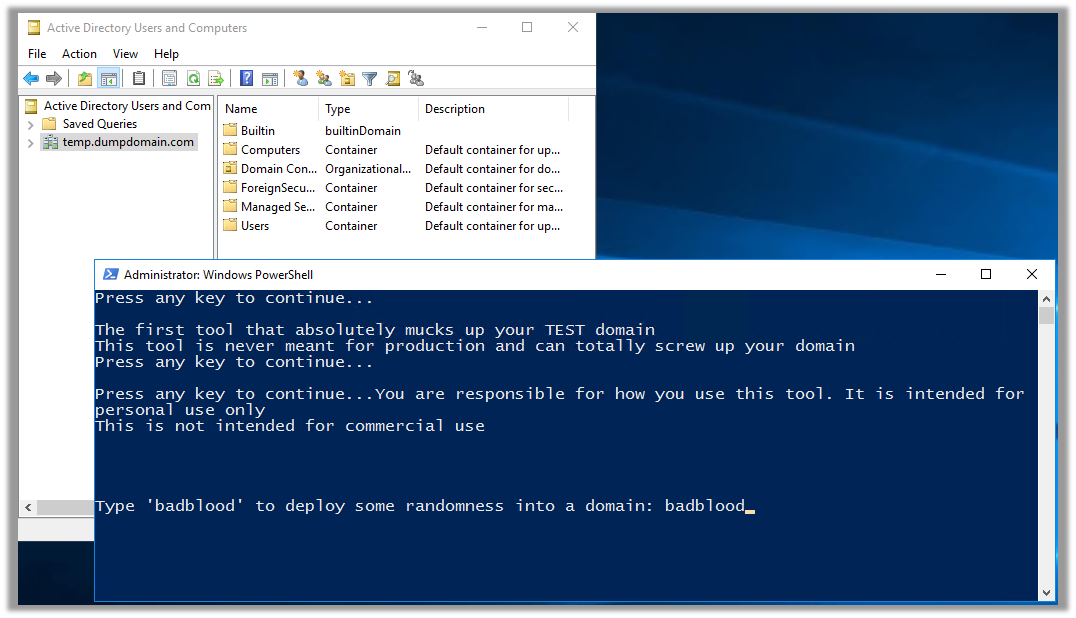
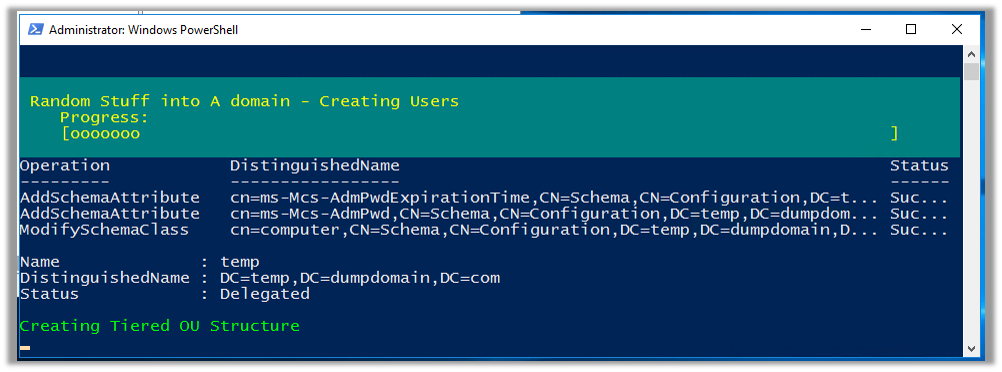
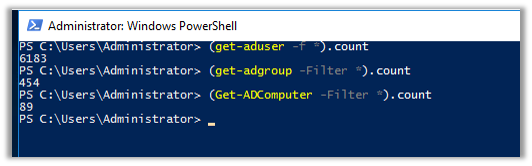
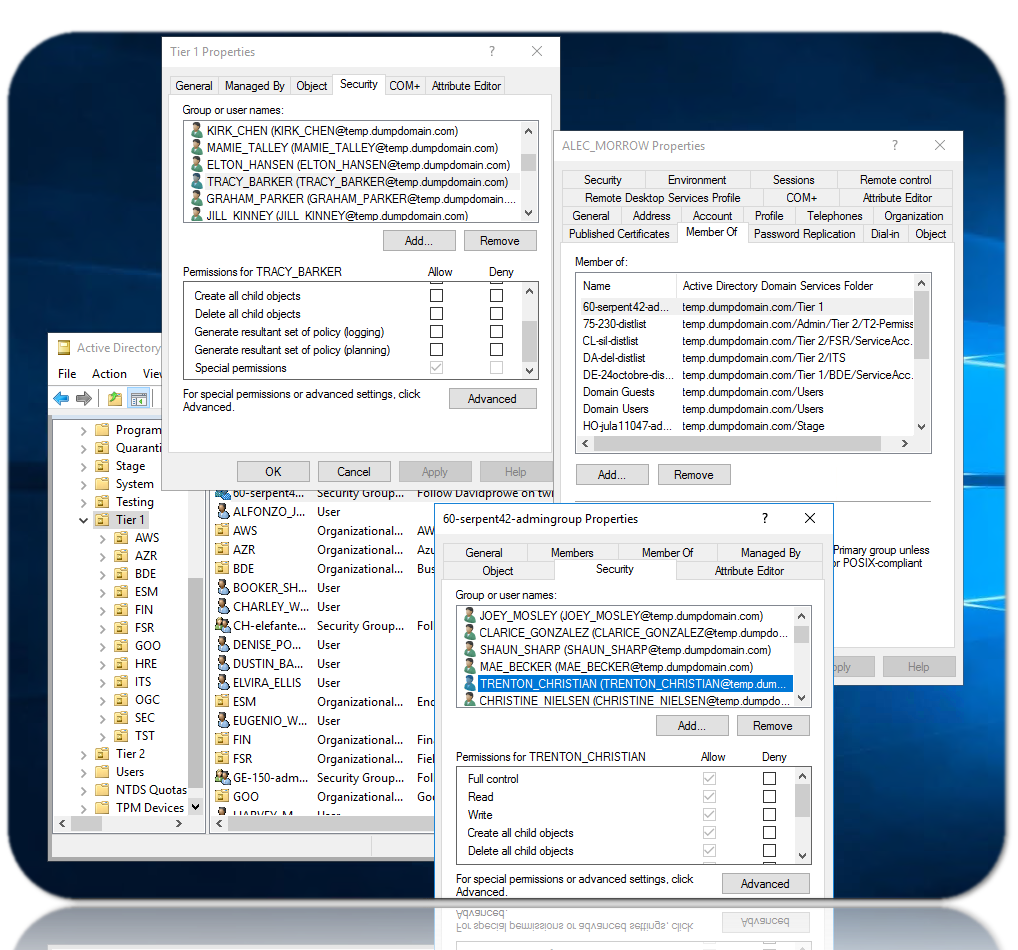
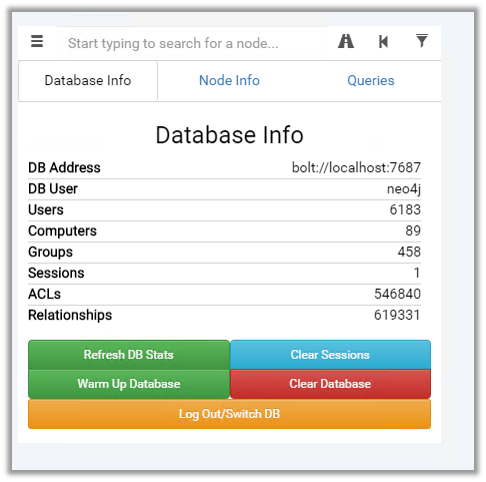
BadBlood by Secframe fills a Microsoft Active Directory Domain with a structure and thousands of objects. The output of the tool is a domain similar to a domain in the real world. After BadBlood is ran on a domain, security analysts and engineers can practice using tools to gain an understanding and prescribe to securing Active Directory. Each time this tool runs, it produces different results. The domain, users, groups, computers and permissions are different. Every. Single. Time.
NONE: At this time all items of the script are configured in the .ps1 files. Files are outlined on the User Guide on Secframe.com
I'd like to send thanks to the countless people who wanted this as a product and waited while I made it!
Requirements:
- Domain Admin and Schema Admin permissions
- Active Directory Powershell Installed
Running On Windows:
# clone the repo
git clone https://github.com/davidprowe/badblood.git
#Run Invoke-badblood.ps1
./badblood/invoke-badblood.ps1
- Message or Follow me on twitter @ davidprowe
- Drop a note on secframe.com
- I am not responsible for cleanup if this is run in a production domain
This project is licensed under the gplv3 License - see the LICENSE.md file for details
Please note: all tools/ scripts in this repo are released for use "AS IS" without any warranties of any kind, including, but not limited to their installation, use, or performance. We disclaim any and all warranties, either express or implied, including but not limited to any warranty of noninfringement, merchantability, and/ or fitness for a particular purpose. We do not warrant that the technology will meet your requirements, that the operation thereof will be uninterrupted or error-free, or that any errors will be corrected.
Any use of these scripts and tools is at your own risk. There is no guarantee that they have been through thorough testing in a comparable environment and we are not responsible for any damage or data loss or time loss incurred with their use.
You are responsible for reviewing and testing any scripts you run thoroughly before use in any non-testing environment. This tool is not designed for a production environment.